
Visibility That Drives Insight
Internet Data and Research
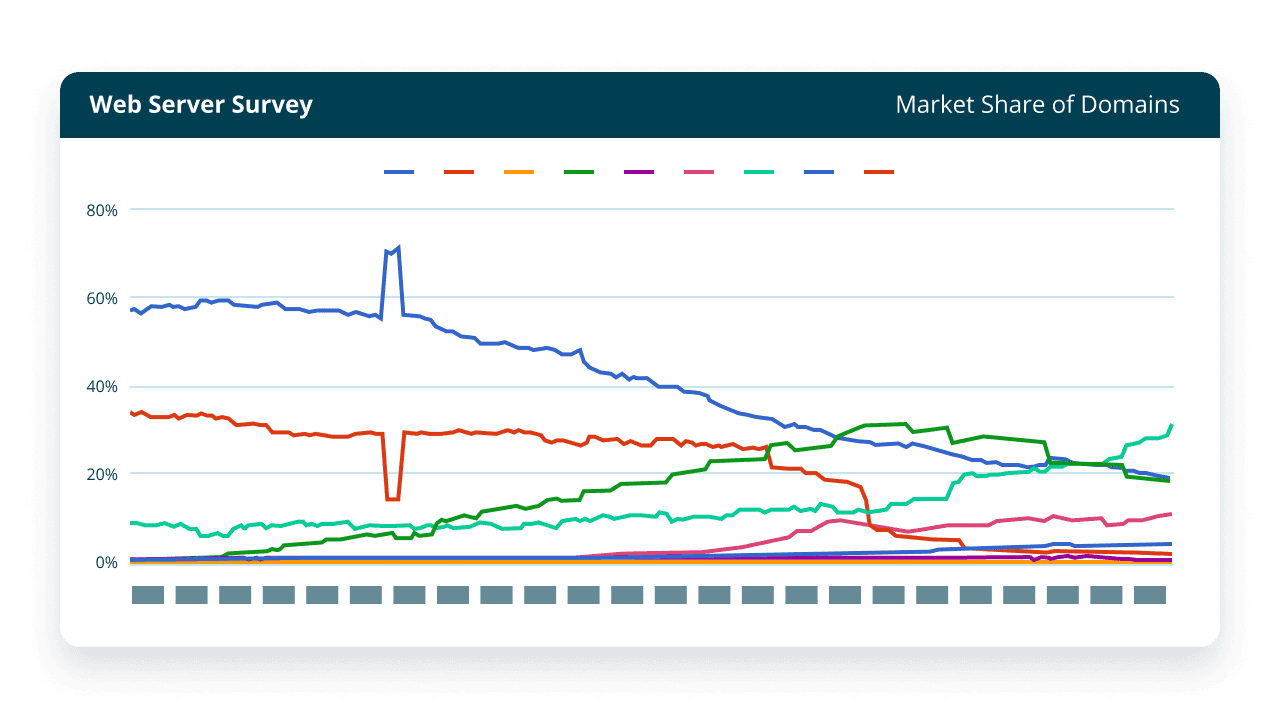
Netcraft has explored the internet since 1995 and is an authority on the market share of web servers, operating systems, hosting and cloud providers, ISPs, certificate authorities, and web technologies. Our internet data and insights inform data-driven decision-making across the entire industry.
Explore the Internet’s Inner Workings
Netcraft has been analyzing the internet since 1995, working with web hosting providers, cloud platforms, certificate authorities, web server developers, ISPs and technology companies to understand its growth and development. Our research improves informed decision-making concerning sales, marketing, expansion and investment in the companies powering the internet.
Netcraft tracks websites, IP addresses, web-facing computers and SSL certificates across the internet. We combine statistics and analysis from our internet surveys with key insights from Netcraft’s cybercrime disruption services. These are presented in web portals, spreadsheets, and in bespoke datasets.
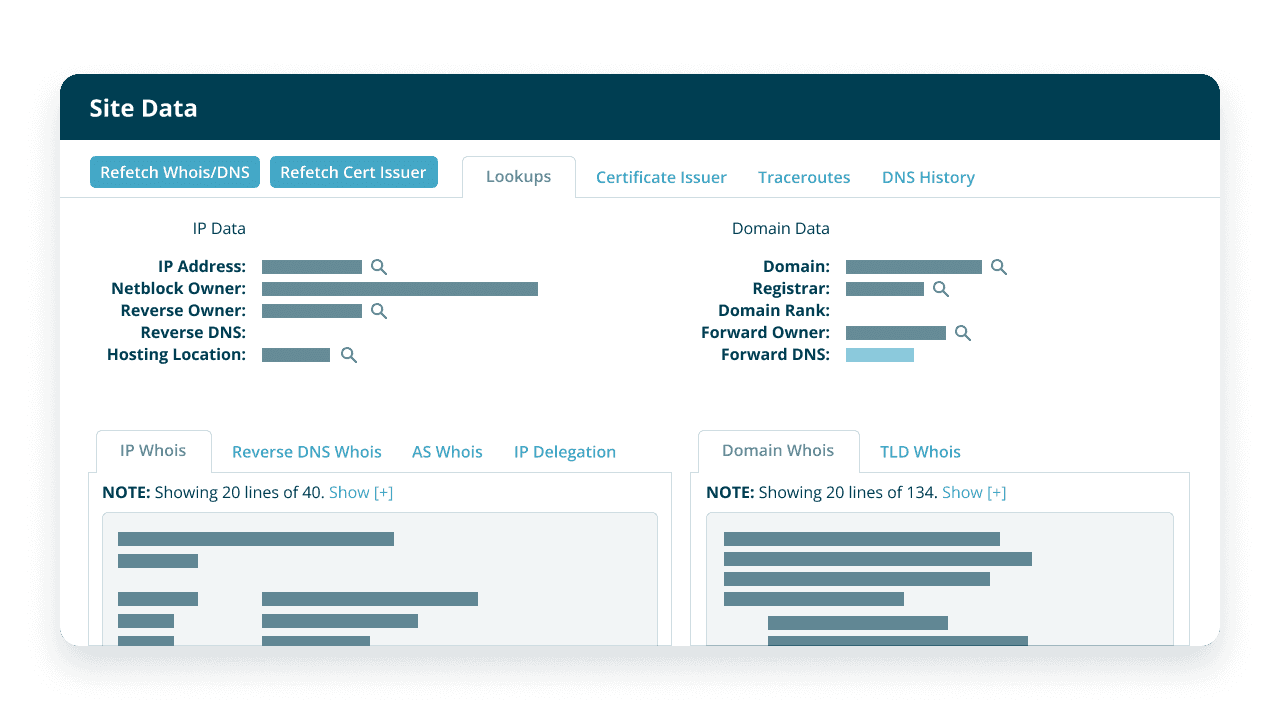
Each website identified by Netcraft is assigned to a hosting or cloud provider using reverse DNS and IP address delegation information. These are grouped to track the parent organizations powering the internet. We track the number of websites, domain names, IPv4 and IPv6 addresses, autonomous systems, SSL certificates, web-facing computers and cybercrime trends for each parent organization.
From large cloud providers to smaller specialist hosting providers, analyzing this information (using data on offered services) presents a unique bird’s eye view of the hosting industry. You can identify global & regional trends and changing market shares – alongside commercial opportunities and threats to your organization.
The TLS protocol (and its predecessor SSL) is used to provide secure communications across the internet. Issued by a certificate authority, SSL certificates authenticate a website’s identity to enable an encrypted connection with the intended recipient that is both private and secure.
Netcraft’s SSL Server Survey has been running since 1996 and has tracked the evolution of SSL, TLS, and publicly-trusted certificate authorities since its inception. You can track the real-world use of certificate authorities, validation types, hosting and cloud providers, and countries alongside HTTPS and TLS features such as HSTS (HTTP Strict Transport Security) and SNI (Server Name Indication) uptake.
Data and statistics from Netcraft’s cybercrime detection and disruption service is combined with internet survey data. This allows you to judge the effectiveness of hosting providers – large and small – in combating the online fraud, phishing and malware running on their own infrastructure.
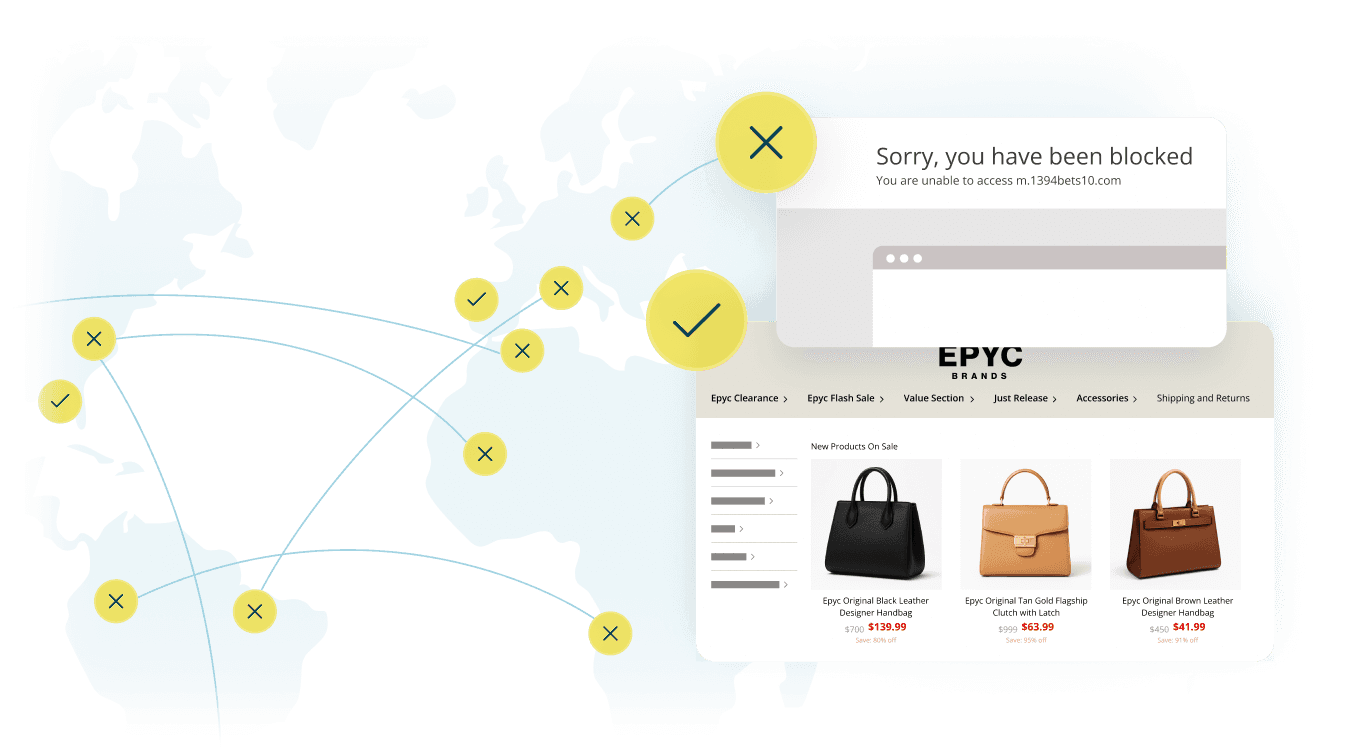
Cybercriminals will often disguise the true location of their hosting network. Data returned from the WHOIS protocol (which can be used to identify IP locations) is self-reported, so can be misleading. Netcraft uses latency measurements and geometry alone to calculate geolocation, which means the genuine location of a web server can almost always be identified.
Explore Our Interactive Platform
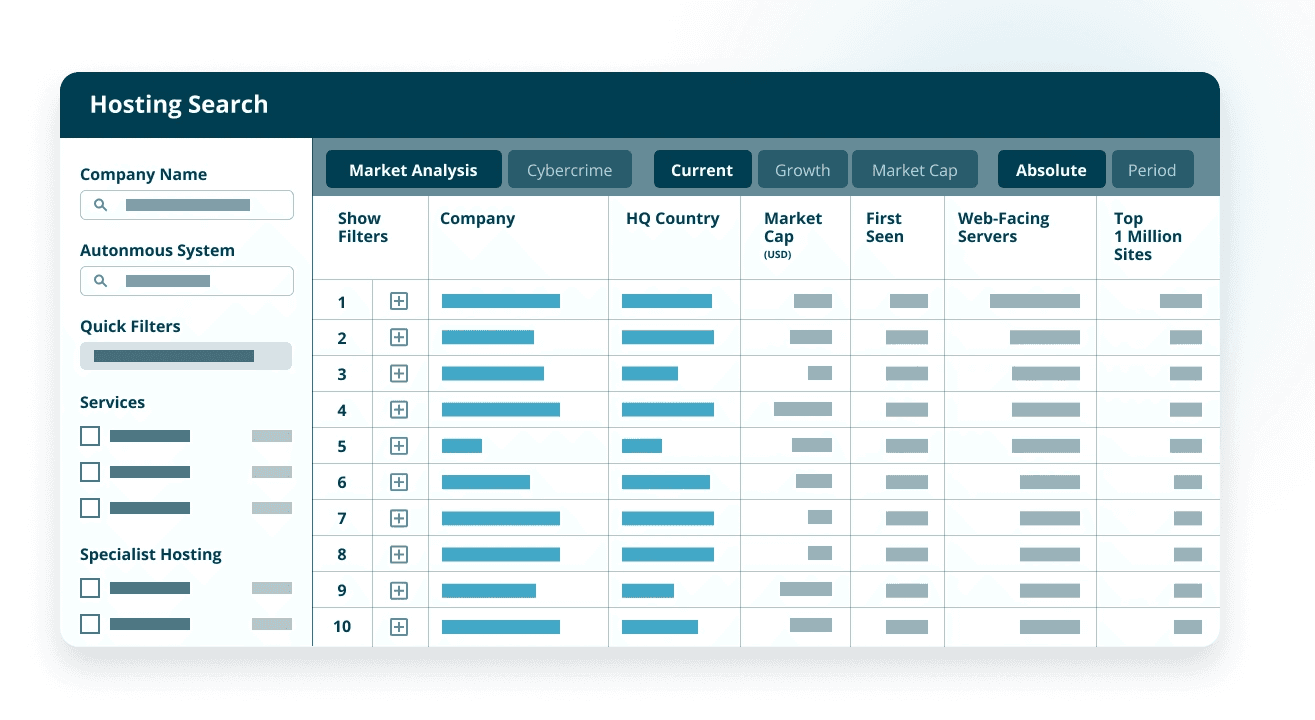
Search, filter, sort, chart, and display Netcraft’s internet data in an intuitive interactive online platform. You can combine the power of search with pre-built tables and charts showing growth over time across a huge variety of metrics including cybercrime, web-facing computers, SSL certificates, hosting provider’s headquarters location, autonomous systems and country.
Additional filtering, corporate relationships, tagging, absolute and relative growth metrics, detailed hosting provider profiles, and export options round out a comprehensive and up-to-date analytical platform. Customers can use Netcraft’s platform to explore the internet’s inner workings, and identify key insights alongside complete historical data.
Frequently Asked Questions
How long have Netcraft been researching what technology is powering the internet?
Using our unique survey methodologies through the Netcraft Web Server Survey, Netcraft SSL Server Survey and related internet censuses, Netcraft has been collecting internet data since 1995. This extended history allows us to observe and report on long term trends and generate meaningful analysis that covers the genesis of almost all modern internet companies and technologies.
How can Netcraft’s research help my organization?
Our comprehensive data analysis gives valuable insights into the growth of hosting companies, cloud providers, certificate authorities, and cutting-edge web technologies. Explore their historical performance, dating all the way back to 1995, and identify the top performers in absolute terms or by percentage.
Track the movements of websites as they transition between hosting providers, technologies, and certificate authorities on a monthly basis and uncover the customers gained and lost by both your business and your competitors. This invaluable information provides a deeper understanding of your customer acquisition and retention strategies, enabling you to make data-driven decisions to enhance your market position.
How can my organization’s analysts interact with the Netcraft datasets?
Interact with the data through the Netcraft web portal. Drill down and filter results in a variety of ways including by country, TLD and popularity. Visualize as a table or chart, or export to integrate into your data analysis workflow. Export data in TSV format for analysis using custom tools, or view detailed company information as a PDF.
How are organizations leveraging the data provided by Netcraft?
The data has multiple use cases across the industry. It’s particularity useful to hosting companies for competitive analysis, mergers and acquisitions, identifying international markets for organic expansion, and also to any organization selling to the hosting industry.
Netcraft provides extensive reports for use in company acquisition and investment due diligence. The reports provide a valuable independent insight into the company’s development and growth, the types of website, technologies and languages used by its customers and also the amount of criminal activity such as phishing and malware hosted on the company’s infrastructure. This can be used to corroborate growth patterns and financial information, whilst also identifying issues such as language requirements for support, a handful of customers accounting for a large part of revenue, poor security or undesirable affiliations.
How can data provided by Netcraft on SSL certificates help organizations?
This data is not just essential to the running of a competitive certificate authority, but is also relevant to a whole host of companies and individuals with an interest in the state of TLS including hardware & software vendors, web hosting companies, SSL certificate resellers, governments and venture capitalists.
How do you calculate the busiest sites?
Each month we determine the busiest sites by the number of visits from users of the Netcraft Browser Extension. This is then combined with detailed hosting information gathered by our Web Server Survey, and compared with the equivalent information from the previous month.
How does Netcraft count distinct web-facing computers?
Netcraft has developed a technique for identifying the number of computers (rather than IP addresses) acting as web servers on the internet, and attributes these computers to hosting locations through reverse DNS lookups.
This provides an independent view with a consistent methodology worldwide on the numbers of web servers, the rate of growth, and the operating systems and web server technology used at each hosting company worldwide.
How do you uncover the real location of a hidden web server?
Rather than relying on self-reported WHOIS data, we can use latency measurements and geometry to calculate location, which means that we have an extremely high degree of confidence in our results.
Performing multilateration on a target involves collecting latency measurements to the target from many different measurement servers across the world, converting those latency measurements into maximum distances from each server, and then using this information to exclude areas which the target cannot be within.
Our multilateration approach relies on collecting latency measurements to targets, which is slower and more expensive than a simple WHOIS lookup. Because of this, we cannot geolocate the entire IP address space ahead of time, so geolocation must be performed on demand (if the result isn’t in our cache). Additionally, the maximum accuracy of our service is dependent on the latency from the nearest measurement server. Residential IP addresses often have too much latency to be geolocated accurately.



