Apps & Extensions
Protection at Your Fingertips
Protect yourself and your organization from cybercrime by using Netcraft’s family of apps and extensions for your browser, phone, and email client.
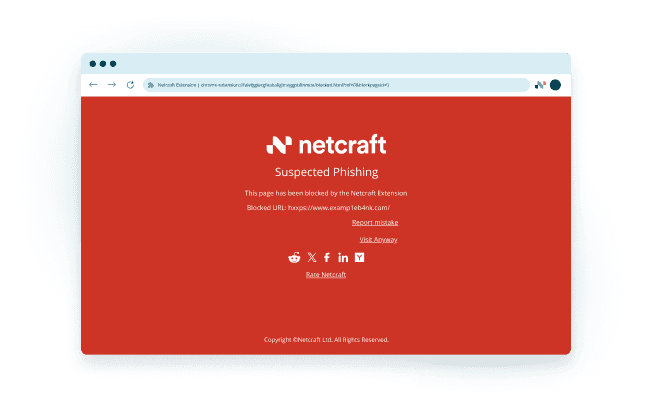
BROWSER PROTECTION
Netcraft’s free browser extension provides real-time enhanced protection from malicious sites defending you from phishing, fake shops, and malicious scripts such as JavaScript skimmers and cryptocurrency miners.
The browser extension works with all major browsers, including Chrome, Firefox, and Edge.
MOBILE PROTECTION
Two-thirds of phishing attacks target mobile users via email and SMS. Many mobile browsers lack complete phishing protection. The Netcraft app extends desktop-level security to your smartphone, instantly blocking new threats. Quickly report suspicious sites and track their status directly within the app. Stay protected wherever you browse.
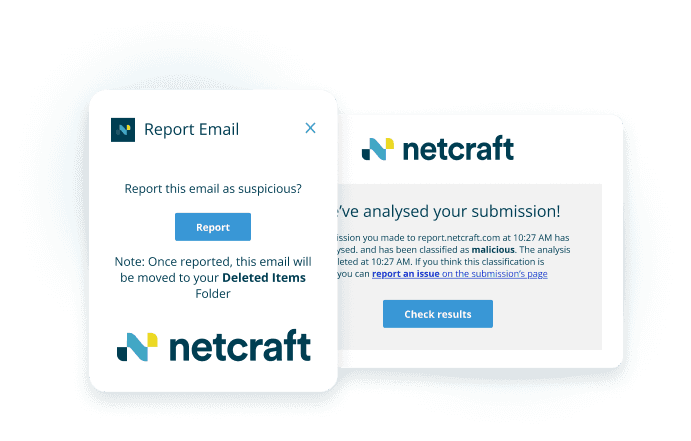
EMAIL PROTECTION
Netcraft’s free email extension allows you to submit suspicious emails to the Netcraft service at the click of a button. All emails are automatically analyzed and validated phishing sites will be blocked in Netcraft’s malicious site feeds, protecting millions of other users from online harms.
The extension runs on Outlook desktop, Outlook Web App, and Gmail.
Protection Against a Wide Range of Attacks
Protect yourself and your organization from cybercrime by using Netcraft’s family of apps and extensions for your browser, phone, and email client.
Frequently Asked Questions
What are phishing websites?
Phishing sites are fraudulent websites that are designed to trick visitors into submitting details such as usernames, passwords, credit card information, or other personal data. Phishing sites are often distributed by email and SMS messages. Any details you enter into phishing sites are collected by the site’s criminal creators.
How do the Netcraft apps and extensions protect me from phishing attacks?
The Netcraft App and extension checks the websites you visit against our constantly updated blocklist of malicious websites, regardless of the device you’re using. If you attempt to visit a known malicious site, a warning is displayed, allowing you to assess the website before you proceed.
What happens when I report a suspicious site?
You can easily report a site that you suspect to be malicious by clicking a button in the Netcraft App, or using the browser extension. Any reports sent to Netcraft are automatically analyzed, and if found to be malicious, the site is blocked in Netcraft’s malicious site feeds, protecting millions of other users.
Which browsers support the Netcraft Extension?
The Netcraft Extension is available for Mozilla Firefox, Google Chrome, and Microsoft Edge.
Which third-party apps are supported by the Netcraft App?
Depending on the platform it’s installed on, the Netcraft App can detect links to malicious sites in the following apps: Facebook Messenger, Facebook, Instagram, Reddit, Slack, Snapchat, Telegram, Twitter, and WhatsApp.
Can I use the Netcraft extension on my desktop email client?
Netcraft’s anti-phishing extension for Outlook can be installed from the Microsoft AppSource. The extension for Gmail is available from the Google Workspace Marketplace.