A REPUTATION FOR ACCURACY
Threat Feeds
Netcraft's digital risk protection feeds give leading global organizations the actionable intelligence they need to stay ahead of evolving digital threats. Built on 23 billion+ proprietary data points analyzed annually, our feeds deliver validated, real-time coverage across 100+ attack types — powering secure activity for billions of users across the internet.

Decades of THREAT DETECTION experience you can trust
Building on years of curated sources, Netcraft ingests 23B+ proprietary threat data points annually.
Actionable Intelligence at Scale
Delivering high-quality insights across 100+ attack types empowers your security team with protection that is both robust and measurably effective.
Namecheap collaborates with Netcraft, a company we identified as a leader in identifying and disrupting cybercrime.
Netcraft Supported Feeds
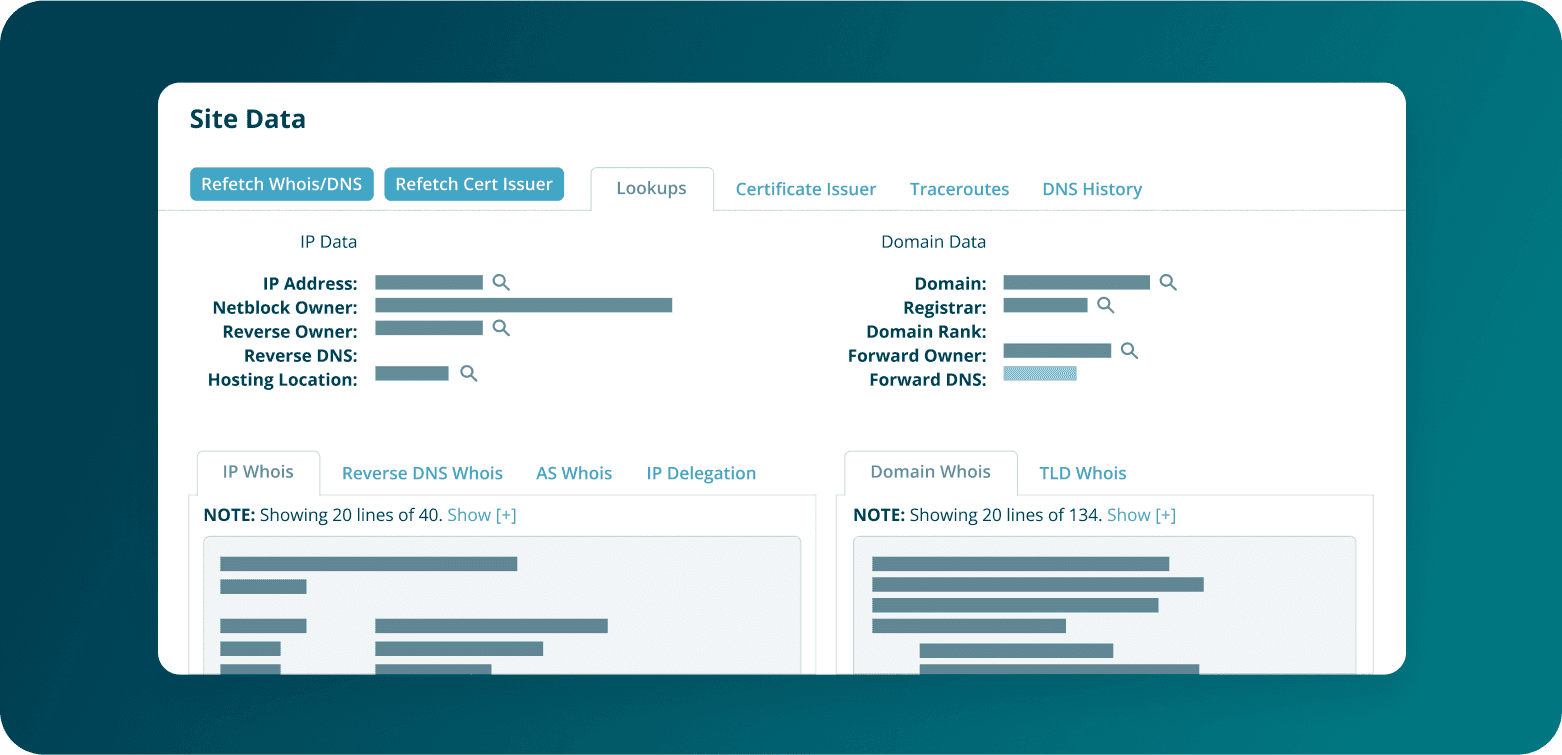
Netcraft’s malicious site and threat intelligence feeds are published delta with new blocks/unblocks every 5 minutes.
Scams
Website-Based
Email-Based
Infrastructure-Based
Blocking Cyber Threats to Downstream Users
Frequently Asked Questions
What makes Netcraft’s digital risk protection feeds more reliable than others?
Netcraft's reputation for accuracy is backed by a proven false positive rate of just 0.02% — one of the lowest in the industry. With 23 billion+ proprietary data points analyzed annually and validation against 100+ attack types, our feeds deliver the trusted intelligence security teams need to manage cyber risk with confidence.
How often are threat feeds updated, and why does that matter?
Our feeds are published delta every 5 minutes, reflecting new blocks and unblocks in near real-time. This rapid cadence is critical — threat actors move fast, and any delay in blocking malicious URLs increases the window for a data breach or exposure of sensitive data for downstream users.
What types of attacks are covered by Netcraft’s feeds?
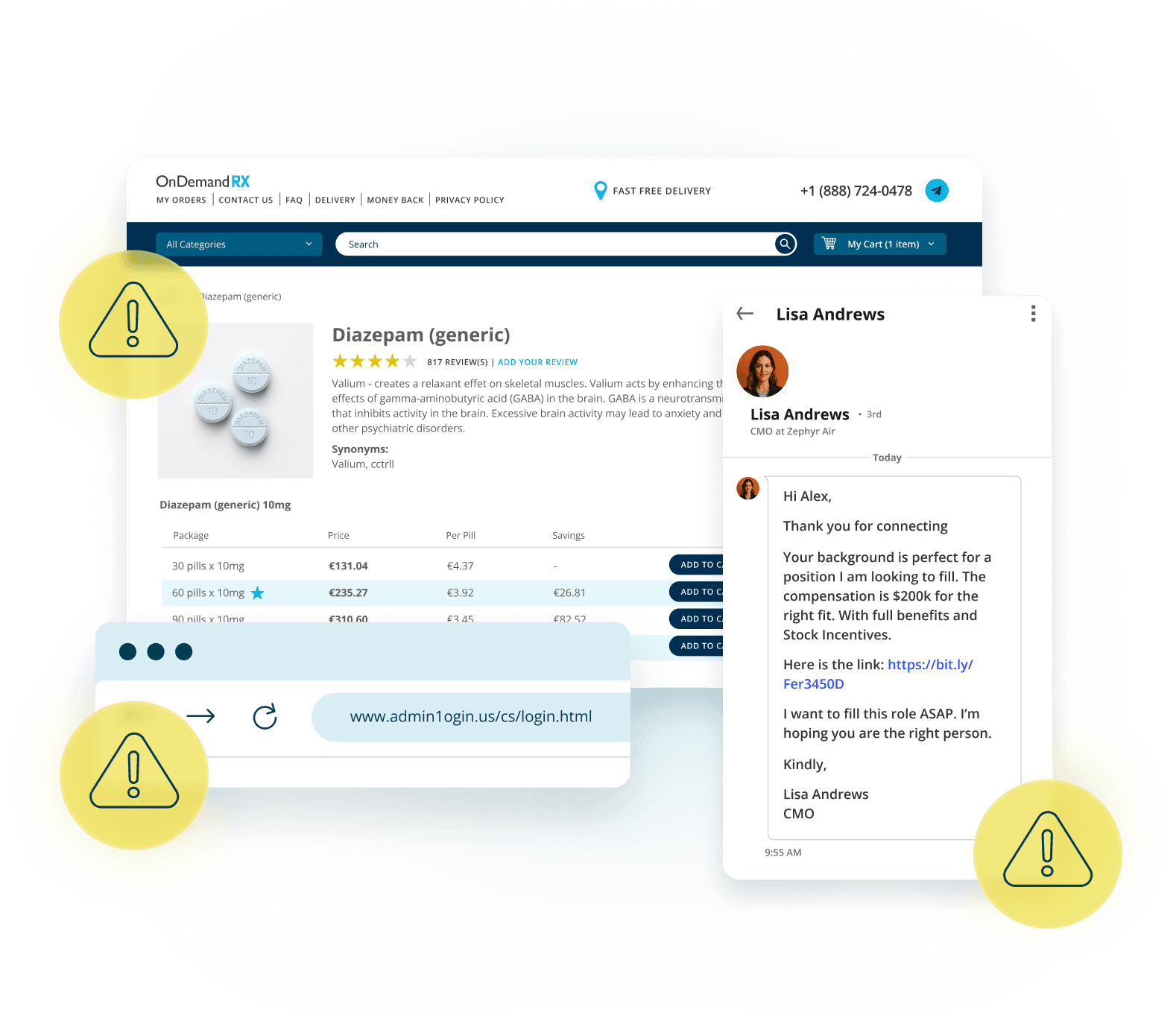
Netcraft provides comprehensive coverage across website-based, email-based, and infrastructure-based threats. These include phishing, support scams, fake shops, web-inject malware, malicious email addresses, cryptominers, and more — spanning over 100 distinct attack types that expose organizations to both cyber risk and brand risk.
How does Netcraft ensure emerging threats are blocked effectively for end users?
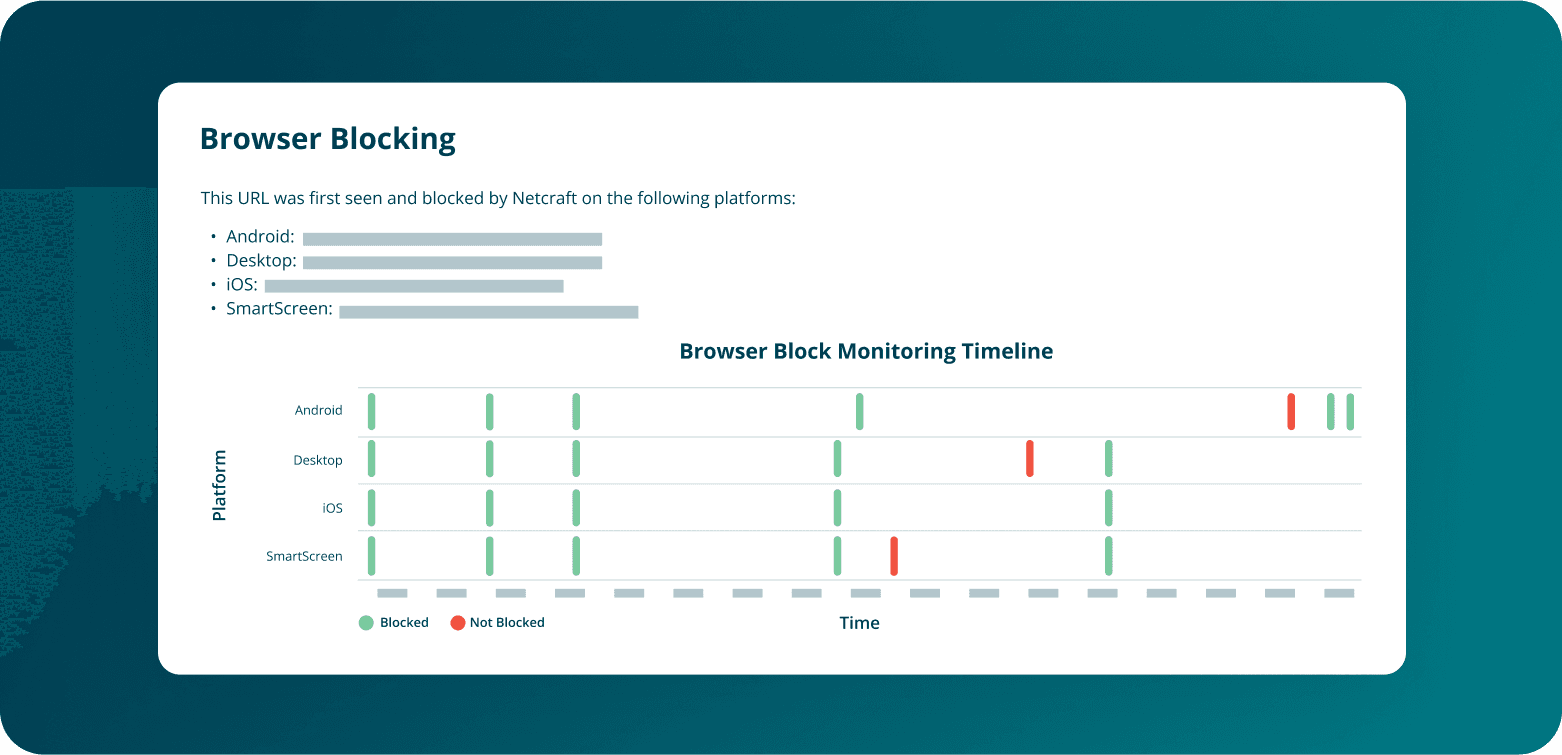
Our fraudcasting process distributes threat intelligence directly to major web browsers and security vendors. Malicious URLs are blocked at scale, preventing threat actors from reaching billions of users worldwide and reducing the risk of sensitive data being compromised. We also monitor infected sites post-blocking to inform subscribers when it's safe to restore access.