Fibergrid’s Rise as a High-Volume Host of Criminal Infrastructure
Fibergrid has operated in the shadows of the internet for nearly a decade. Since Netcraft conducted its first takedown against a Fibergrid-hosted site in 2018, the provider has evolved into a persistent and high-volume bulletproof hosting network. Netcraft has identified 16,700 currently active fake shops on Fibergrid-linked infrastructure, used to defraud customers at scale.
In this investigation, we pull back the curtain on how Fibergrid’s infrastructure has been leveraged to support large-scale criminal activity, from stolen African IP address space to a maze of shell companies, proxy ASNs, and strategic misdirection designed to evade disruption.
How Stolen African IP Space Became the Backbone of Fibergrid’s Infrastructure
Fibergrid’s unusually large pool of IPv4 address space is one of the primary foundations of its scale. Much of that space traces back to what is commonly referred to as the Great African IP Address Heist, a scandal uncovered in 2019 when a MyBroadband report alleged that a former AFRINIC executive was involved in improper re-registration of IPv4 addresses to offshore companies by manipulating WHOIS records.
Today, Fibergrid still controls three of the stolen AFRINIC-issued ranges, representing one million IPv4 addresses, valued at 20-25 million USD.
The AFRINIC-issued ranges controlled by Fibergrid are as follows:
196.196.0.0/14
196.56.0.0/14
196.240.0.0/13
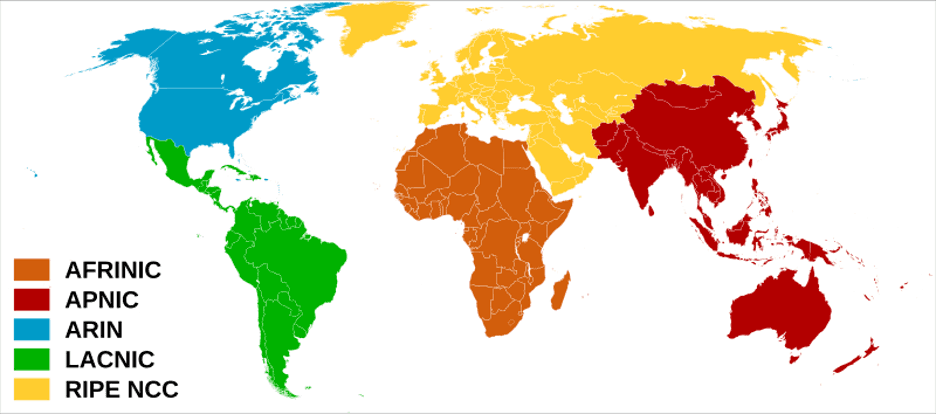
Figure 1. Regional Internet Registries, https://commons.wikimedia.org/wiki/File:Regional_Internet_Registries_world_map.svg.
AFRINIC policy requires that address allocations be justified for services originating from the AFRINIC service region. However, Netcraft's observation of Fibergrid suggests a different infrastructure footprint.
Multilateration Reveals Fibergrid’s Real Global Footprint – And It’s Not in Africa
Although Fibergrid claims to be based in the Seychelles—and relies on this claim to justify its AFRINIC allocations—Netcraft’s multilateration tests don't support this claim.
Using latency measurements from vantage points across the world, Netcraft estimated the physical location of Fibergrid-linked servers. In cases where location could be determined with high confidence, the identified infrastructure was always outside Africa:
Country | IP Addresses Identified |
United States | 1,122 |
United Kingdom | 606 |
Netherlands | 544 |
Canada | 349 |
Sweden | 116 |
Estonia | 65 |
Poland | 7 |
Based on these multilateration tests, we can sometimes infer more precise locations for these Fibergrid servers, such as in this case of Fibergrid’s Canadian hosting infrastructure:
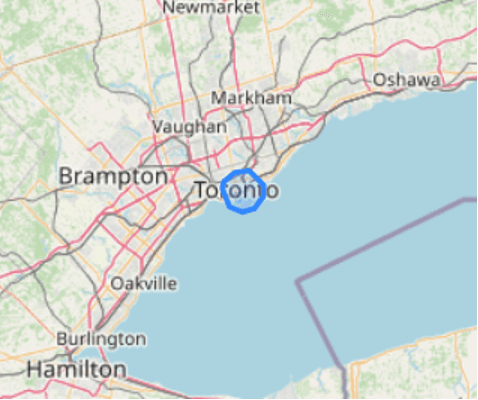
Figure 2. Example of precise location inferences in Fibergrid's Canadian hosting infrastructure.
Some of Netcraft’s geolocation servers are located within Equinix TR2, a data center in Toronto. Their low latency measurements suggest that some Fibergrid-linked infrastructure is located in or very near Equinix TR2. Measurements suggest Fibergrid-linked infrastructure in or very near Equinix colocation facilities across many of their other regions: Los Angeles, Atlanta, London, Amsterdam, Stockholm, and Warsaw.
The data suggests a clear conclusion: Fibergrid leverages African IP space but operates almost entirely in Europe and North America, a key discrepancy that AFRINIC could leverage to justify taking action. Its presence in Western infrastructure introduces potential enforcement opportunities for law enforcement agencies outside of Africa.
A Web of Shell Companies Built for Evasion
Like many bulletproof operators, Fibergrid hides behind a shifting constellation of companies designed to obscure attribution and complicate takedown efforts.
The core organizational entities on the Internet used to decide where to route your data are called autonomous systems (ASes). Netcraft has linked Fibergrid operations to at least the following AS numbers:
AS37518 Fiber Grid INC
AS41564 Orion Network Limited
AS46805 Angelnet Limited
AS48950 Global Custom Data Limited
AS57858 Angelnet Limited
AS58065 Orion Network Limited
AS60485 Angelnet Limited
AS63119 Angelnet Limited
AS205056 DIAHOSTING LIMITED
One entity appears to act as an upstream or intermediary network: Orion Network Limited, which maintains upstream transit relationships and provides connectivity to ASes that Netcraft has observed hosting malicious activity.
This complex web of ASes is reflected in the companies registered to and associated with Fibergrid’s operations. The complexity can complicate attribution and enforcement efforts. We have mapped out a slice of these companies, correlated through shared registration details and directors:
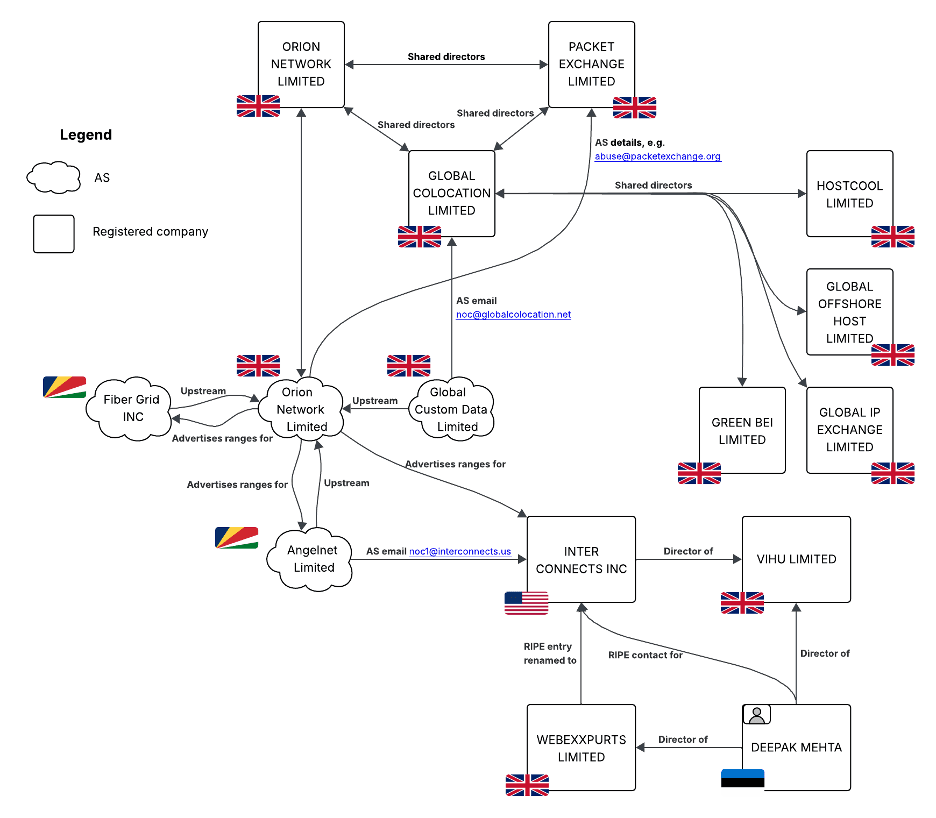
Figure 3. A slice of infrastructure linked to Fibergrid.
This analysis identifies additional company names associated with the same network:
Inter Connects Inc
Global Colocation Limited
Packet Exchange Limited
Webexxpurts Limited
Vihu Limited
Hostcool Limited
Global Offshore Host Limited
Global IP Exchange Limited
Green Bei Limited
The vast majority of these entities are incorporated in the UK, consistent with observations of infrastructure located outside Africa. The UK company registration system has characteristics that can and have been misused by cybercriminals such as:
Minimal verification: Companies House has historically not verified all submitted information, though reforms are underway.
Low cost: Until 2024, incorporation cost just £12.
Disposable structure: Entities can be abandoned after use; IP and ASN allocations persist.
One of Fibergrid’s registrations was in Estonia, which offers company registration benefits that can enable shell company operations. Estonia has pursued becoming the world's "most digital country", leading to a company registration system designed for automation and scale. AML oversight can suffer as a result. Additionally, Estonia's e-Resident programallows individuals anywhere to register a company in Estonia, allowing remote administration with a gateway to EU corporate legitimacy. Checks applied to foreign owners are limited because e-Resident companies are largely treated as domestic.
Estonian and UK company registrations have previously been used together to provide corporate legitimacy with minimal reporting, transparency, and regulatory obligations. In September 2020, the International Consortium of Investigative Journalists (ICIJ) reported on a system of UK shell companies run through Baltic states to allow opaque ownership and banking with weak AML. The UK provided the legal corporate legitimacy while Estonia provided banking and digital infrastructure access. While some remediation to these systems has been done following the ICIJ's findings, the main issues remain to some degree, as seen with Fibergrid.
The hosting providers associated with malicious activity to which Fibergrid has distributed address space can also be clustered with additional malicious hosting providers by shared corporate officers. In a cluster of ten UK-registered hosting companies, there has been a rotating cast of directors consisting of the same eight individuals. Additionally, six of these companies have at some point had a corporate director of Digitas LLC.
Digitas LLC is registered in the US, being formally incorporated in Delaware. Delaware has been criticized for limited public beneficial ownership transparency. Additionally, the US Federal Government's Corporate Transparency Act (2025) has removed the requirement for almost all domestic companies to report beneficial ownership information. While contradictory to Fibergrid's claims to be based in Africa, this US registration can be abused to slow document requests, shield information, or avoid disclosures that would be legally required to operate in other jurisdictions.
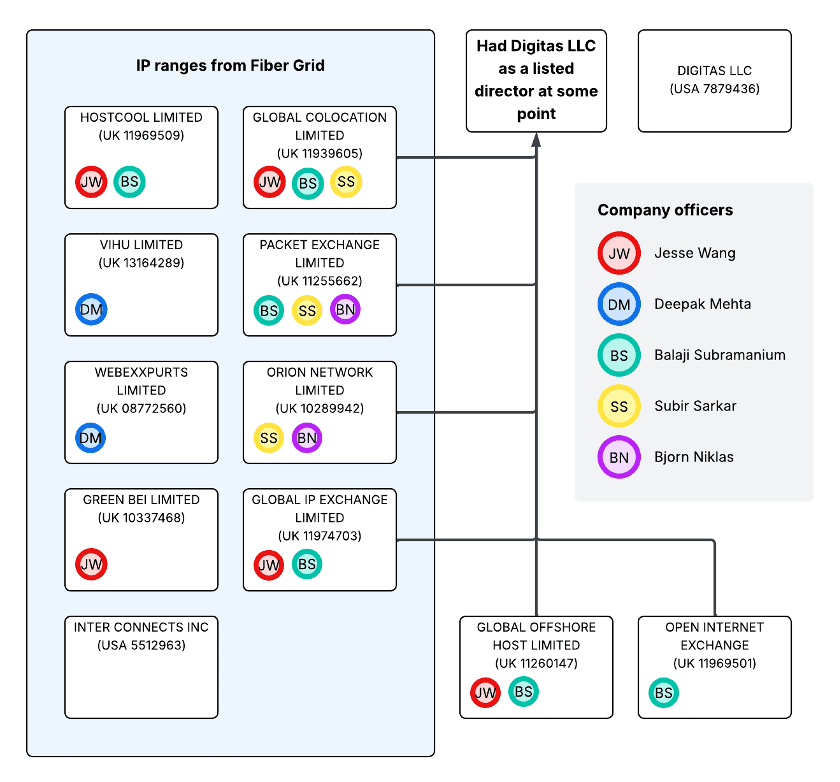
Figure 4. Network of companies and shared directors linked to Fibergrid’s infrastructure.
Fake Shops: A Primary Use Case Observed on Fibergrid Infrastructure
Fake shops are the dominant activity observed on Fibergrid-linked infrastructure. While we continue to detect Fibergrid-hosted phishing sites and health product scams, counterfeit and fraudulent e-commerce operations are overwhelmingly the largest category, representing nearly 70% of all attacks hosted on Fibergrid-linked infrastructure we’ve disrupted in the past 12 months.
Fake shops are online stores that mimic legitimate e-commerce platforms to trick consumers into making fraudulent purchases or stealing their sensitive data. These stores will either not deliver any products at all or deliver counterfeit goods while stealing the victim’s money. The sites will often be engineered to appear in standard search engine results, as well as be part of social media and search engine advertisement campaigns, listing heavily discounted products to attract end-users away from legitimate platforms and onto these malicious fakes.
As the sites rely more heavily on organic traffic, rather than the short half-life email and text campaigns used in phishing, bulletproof hosting providers like Fibergrid that provide criminals with more robust hosting are particularly valuable.
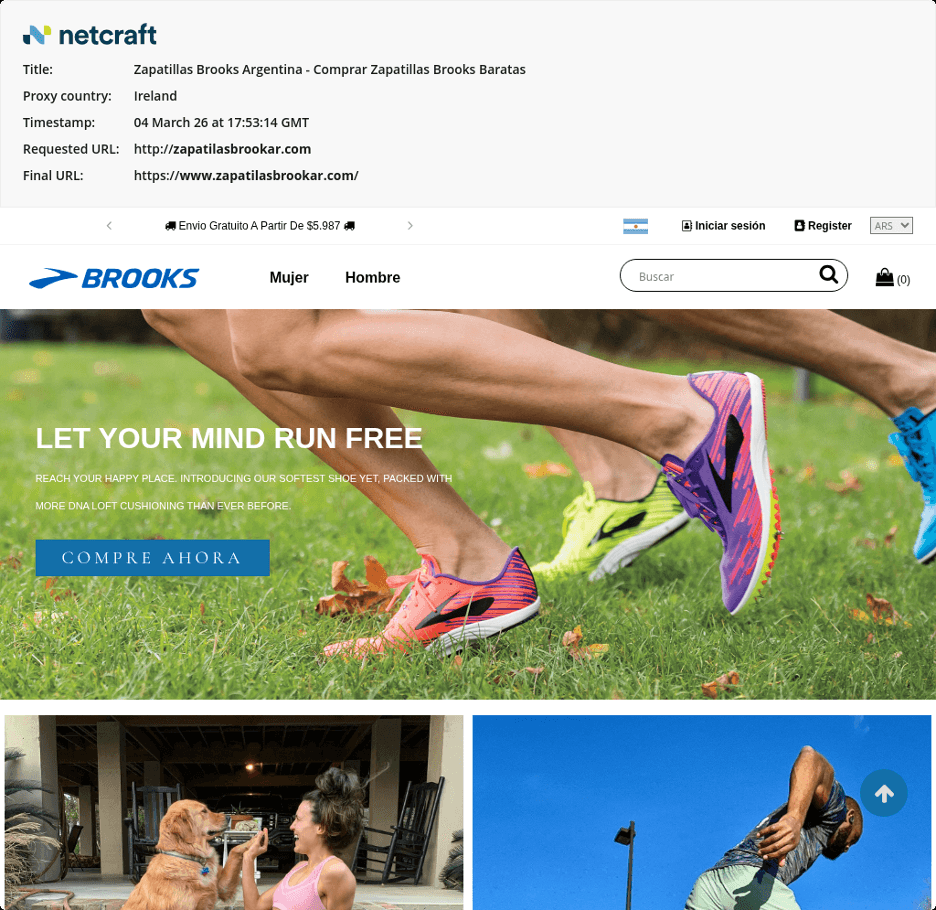
Figure 5a.
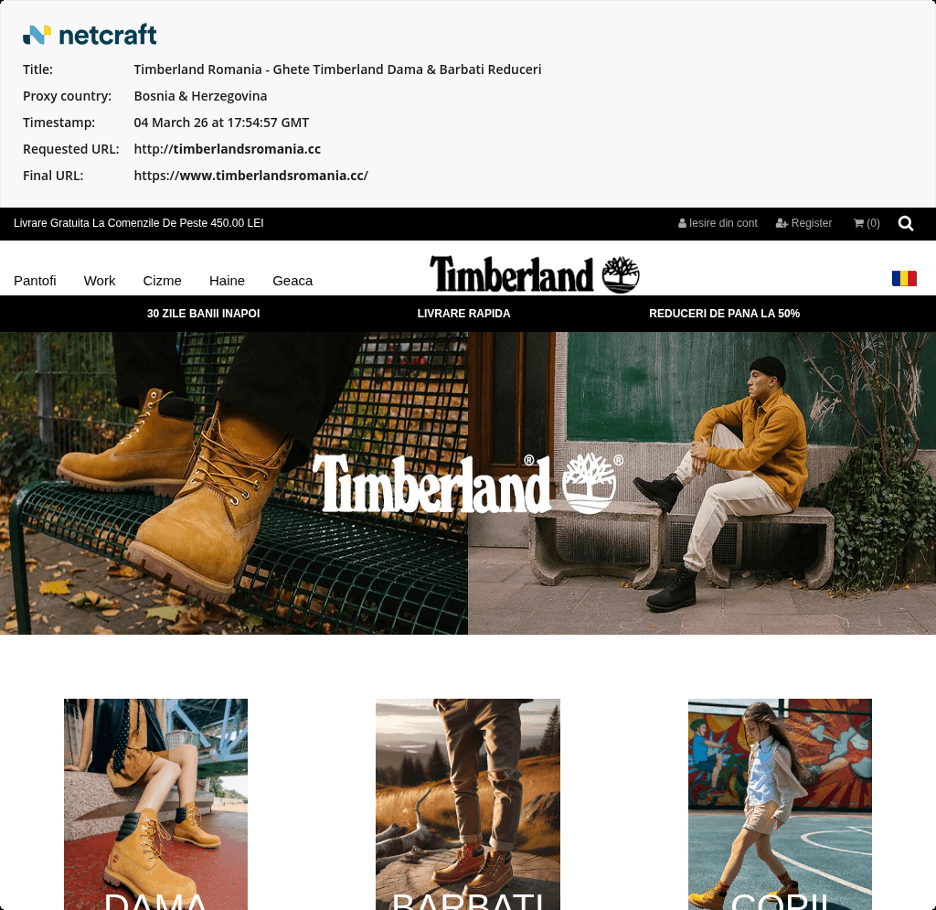
Figure 5b.
Figures 5a. and 5b. Fake shops hosted on Fibergrid.
Looking at a small sample of domain registrations pointing at Fibergrid suggests that fake shops are the lifeblood of this infrastructure.
Domain | Registration date | Description |
zapatilasbrookar[.]com | 2026-03-04T11:04:08Z | Fake shop targeting Brooks |
timberlandsromania[.]cc | 2026-03-04T10:48:41Z | Fake shop targeting Timberland |
bratziezpuertorico[.]com | 2026-03-04T08:14:47Z | Fake shop targeting BRATZ |
airupfranceshop[.]fr | 2026-03-04T08:14:00Z | Fake shop targeting Air Up |
airuppullosuomi[.]com | 2026-03-04T02:32:18Z | Fake shop targeting Air Up |
air-upsuomi[.]fi | 2026-03-04T02:28:09Z | Fake shop targeting Air Up |
airupsweden[.]com | 2026-03-03T18:15:33Z | Fake shop targeting Air Up |
pinkpalmpuffnetherland[.]com | 2026-03-03T10:27:34Z | Fake shop targeting Pink Palm Puff |
ultimateearsindia[.]com | 2026-03-03T09:57:01Z | Fake shop targeting Ultimate Ears |
The above domains were registered in a little over 24 hours and are all fake shops targeting a variety of brands. During this period, Netcraft did not observe a single legitimate domain registered that was pointed at Fibergrid.
Where Fibergrid Can Be Disrupted: Upstreams, Registries, and AS-Level Pressure Points
Despite its resilience, Fibergrid is not untouchable. Netcraft’s analysis highlights several direct pressure points that we can leverage.
1. Upstream Provider Intervention
Cutting off transit routes removes Fibergrid’s most critical lifeline. The “clean” intermediary ASNs should be targeted to undermine Fibergrid’s strategy of distancing itself from malicious activity.
2. Regional Internet Registry (RIR)-Level Action
Geolocation and organizational inconsistencies present opportunities for AFRINIC and other RIRs to review and revoke improperly held resources.
3. Domain-Level Action
Even if fraud is hosted by Fibergrid, fraudsters still need domains to facilitate their campaigns, allowing the attacks to be disrupted through domain registrars and registries.
Unfortunately for these fraudsters, Netcraft has deep relationships with key registrars and registries, allowing for quick and scalable disruption at the domain-level.
4. Fraudcasting
Simultaneously, while going after these attacks at the hosting and domain-level, end-users can be immediately protected by the indicators of compromise (IOCs) being shared with providers who are able to intercept requests to these fraudulent sites. These providers include browser vendors, DNS operators, and anti-virus providers.
Fibergrid’s Future as a Criminal Host Depends on Its Ability to Stay in the Shadows
Fibergrid is emblematic of infrastructure frequently associated with modern criminal hosting operations: geographically distributed, legally fragmented, and structurally designed to resist disruption. Yet each layer of that structure, from stolen IP blocks to proxy ASes, is a potential point of intervention once exposed.
Netcraft continues to monitor Fibergrid’s behavior, automate large-scale detection of Fibergrid-hosted attacks, and work directly with providers to dismantle the network’s ability to operate at scale.