Executive Summary
Passkeys are a clever mechanism for phishing-resistant credentials that verify the user, the device, and the service.
Organizations looking to implement passkey solutions should be aware of risks during the transition period and consider their needs when it comes to fallback password use, storage safety, and usability.
It is likely that attackers adapt tactics when looking to exploit services using passkeys. Knowing these attack types during the transition to passkeys is important to be aware of your changing attack surface.
No passkey solution will be completely phishing resistant while parts of it still rely on passwords and non-phishing resistant credentials.
What are Passkeys and Why Do They Matter
Passkeys are one of the most highly recommended and secure authentication options while allowing users to forgo password memorization. The standard allows for device-based authentication to confirm identity without relying solely on the user’s input, making it phishing resistant as well.
Passkeys first became broadly supported in 2022, with passkey support announced for iOS, Android, Chrome, and Windows. Adoption has only increased, with 98% of desktop devices and 95% of mobile devices supporting passkeys as of Q2 2025. As this option sees increased adoption, it is important for users and industry to be aware of the fraud tactics that can still affect and exploit passkey users.
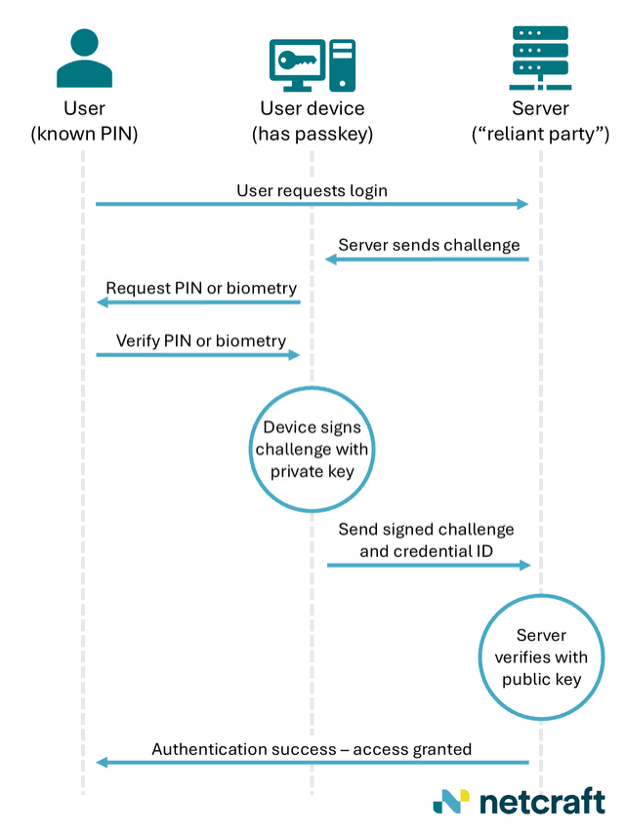
Passkeys promise phishing resistance and an easy user experience. They do this by combining user information (perhaps a PIN or fingerprint) with information about where the passkey is stored and the exact domain that the passkey is meant to be used with. This allows a user to authenticate their own identity and the domain owner’s identity at the same time using public key cryptography. This clever mechanism allows multiple types of authentication while being something difficult for the user to share with outside parties and unusable by other endpoints, making it phishing resistant.
While this is a major step forward from passwords and appears to be minimally invasive to users, every new defense leads to new attacks being developed. The transition to passkeys is likely to be slow, rocky, and vulnerable to modified versions of the same attacks that have been used against password-protected resources.
When and How Passkeys Fail
As with many security solutions, the strength of its implementation has to be balanced with usability by the average user. In the case of passkeys, this often shows up in their recovery options. Where recovery is secure but difficult, usability suffers and where recovery is as friendly as traditional password recovery often is, this can undermine the phishing resistance of passkeys.
Several passkey implementations have had their security undermined by the ease of their recovery process. According to the FIDO Alliance, the group behind the passkey standard, the transition phase between password-based authentication and passkey-based authentication is likely to result in partial prevention of phishing. This would not incorporate the level of phishing resistance that passkeys can offer when implemented in accordance with best practices. However, the adoption curve means that this ideal implementation is highly likely to remain uncommon in the near future and certain attack types fitted to these non-ideal early adoptions are almost certain to persist during the transition period.
The FIDO alliance has identified four main implementation flaws that could be used for exploitation during this transition period.
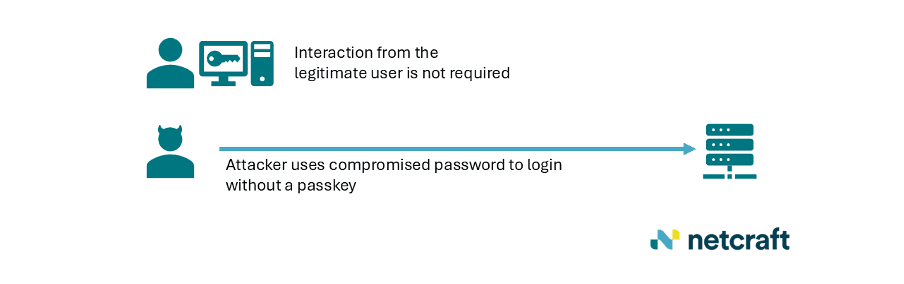
Allowing passwords as an alternative login method
If passkeys are made available but not required as the only sign-in method, they can easily be bypassed. This implementation may be used to enable user adoption in the early stage of passkey rollout but does not effectively add any security to the authentication process.
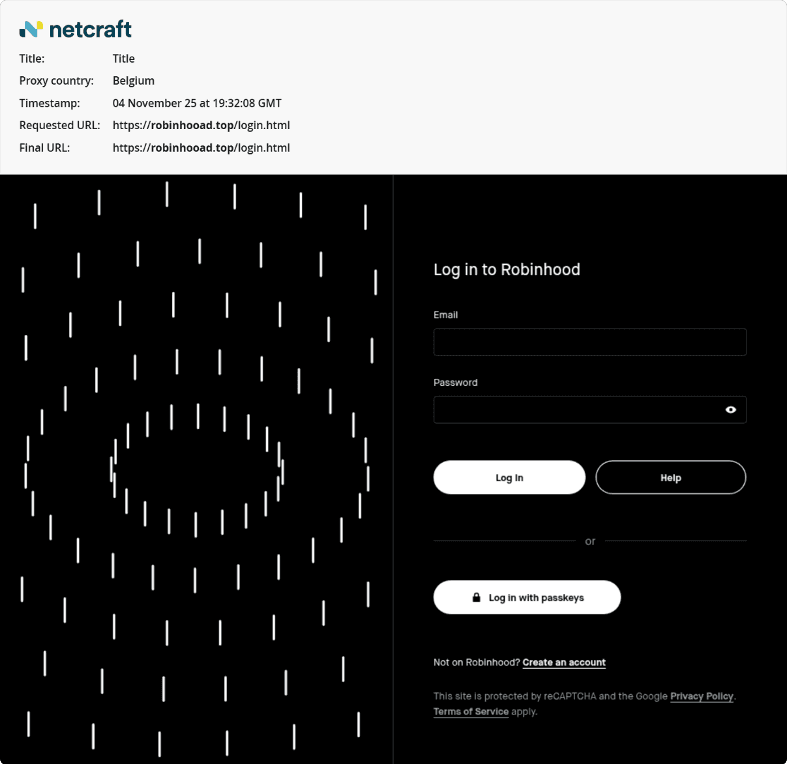
Netcraft has observed phishing sites which reference or request passkeys as a login option. In some cases, this is just a result of copying the legitimate website and, in doing so, carrying over their WebAuthn reference. However, as passkeys are tied to local device information, any recovered user passkey information would be unusable by the attacker. Where passkey options are shown as available on copied phishing infrastructure, this demonstrates the weakness of authentication that allows both login methods. Though the legitimate service allows passkey use, its continued use of password-based authentication makes this service continue to be vulnerable to password phishing. The number of services that have fully switched to only passkey-based authentication is currently very limited.
The phishing site example below showed a passkey login option as this is included in the login portal it is imitating. Though passkeys are an available login option, this phish would have been able to compromise Robinhood accounts through traditional login credential theft. This phishing site is no longer active.
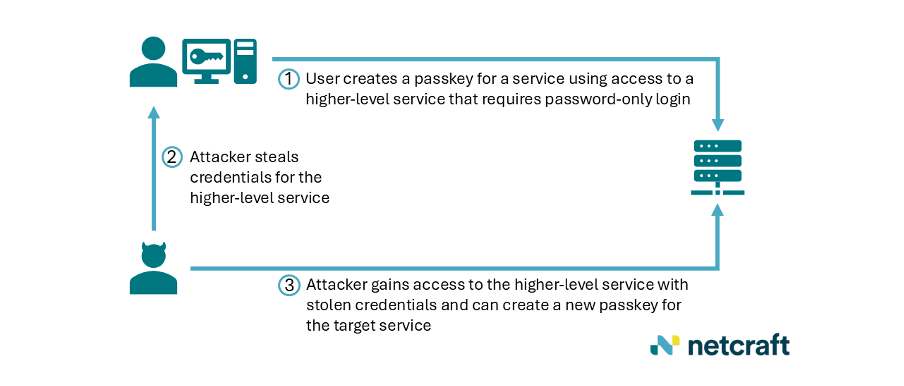
Allowing passkey creation using only phishable credentials
In cases where centralized resources are accessed by passwords but specific functions require passkeys, there is a potential weakness where these passkeys can be created with only password-based authentication. This undermines the phishing-resistance of passkeys by making them a downstream product of authentication that isn’t phishing resistant.
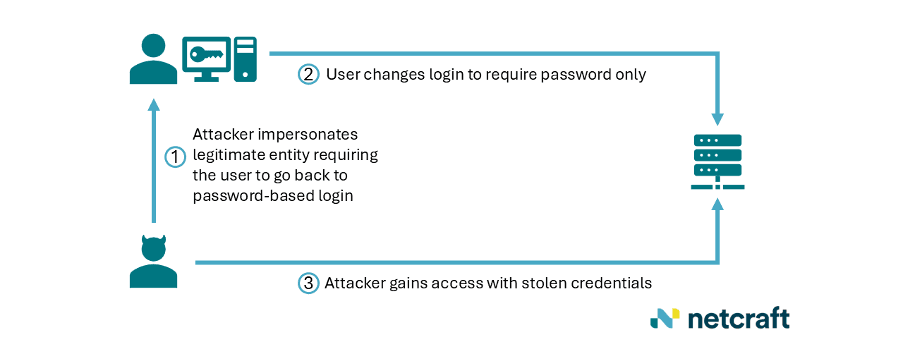
Allowing security option downgrade
If a passkey is the sole sign-in method but others can be configured, a user may be targeted with social engineering to downgrade their login method to a less secure authentication method, such as passwords. Though this attack method is a less likely option compared to the others highlighted by the FIDO alliance, it is still notable as a viable method of bypass.
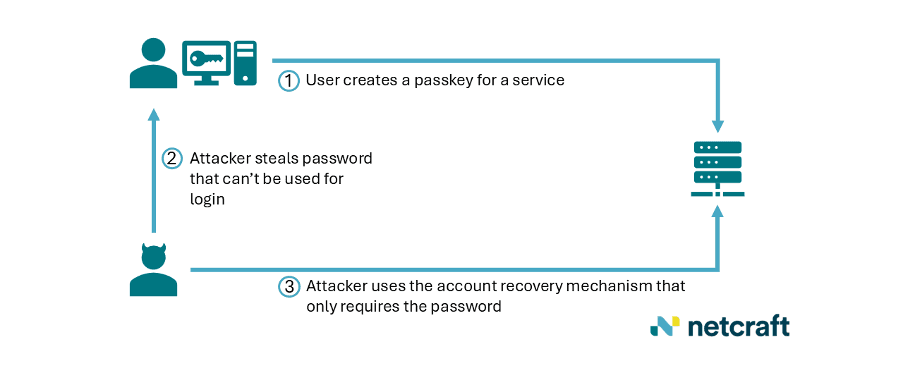
Account recovery with weak authentication
This method is likely to become the most used of those highlighted by the FIDO Alliance for exploitation of systems that allow passkeys but haven’t completely outgrown passwords yet.
Where passkeys are the only authentication option for sign-in but reset of them relies on older, less phishing resistant methods, this mechanism can be exploited by attackers using the same methods that have been effective against password-based authentication. The methods of authentication for account recovery could include passwords, security questions, or SMS verification, all of which have known issues.
What to Expect Next
Non-phishing based threats remain, such as device theft. If an unlocked device is stolen and the PIN is known, passkeys may be used by an attacker. However, this scenario is rare and would be expected to be highly impactful otherwise as well.
As with many types of phishing-resistant design, the fact that passkeys can resist phishing is based on the inability of the user to directly access the resource that being targeted. While this is an effective method when implemented as the user’s sole option, this intentional cut to user permissions may hinder adoption among those who feel that they cannot recover their passkeys or have as much control as they do with passwords. Having a transition phase to passkeys will allow an easier switch for users not ready to give up their more familiar login methods yet. However, this cannot grant true phishing resistance and will be vulnerable to the attacks mentioned above until a system is passkey-only.
As for the security of passkey storage itself, this requires trusted devices or tools. These are validated as compliant by the FIDO Alliance, the same group that created the original standard for passkeys, in the FIDO Alliance Metadata Service. It is worth noting that the FIDO Alliance is a closed industry group, unlike many technical standards bodies. Their membership fees and opaqueness have led to friction with some would-be open source contributors who have not been able to fix errors. In one case, a member of the W3C WebAuthn project, which created the standard for FIDO2 browser support, mentioned being unable to remove Bitwarden from the trusted entity list for passkey storage. This was despite their non-compliance since Bitwarden can use passkeys without prompting the user to re-enter a PIN or provide biometry. Though Bitwarden is still considered a strong password manager, examples like this show the issues that closed standards consortiums could create for transparency during the adoption period. FIDO2 compliance may rely on external verification in addition to the official list of trusted storage solutions.