Summary: DMCA takedowns were designed for copyright disputes, not phishing infrastructure. While legal notices can remove copied content, AI-generated phishing campaigns can steal credentials, rotate domains, and relaunch attacks long before legal review processes finish. Technical disruption stops phishing differently by identifying and neutralizing malicious infrastructure before attackers can scale harm.
Table of Contents:
A convincing phishing site once required time, effort, and technical skill. Attackers had to copy branding, recreate workflows, and manually build infrastructure. That friction created opportunities for defenders to react.
Today, AI-generated phishing campaigns operate at industrial scale. According to Security Boulevard, nearly 82.6% of phishing emails now use AI language models or generators — and achieve a 60% overall success rate against humans, with 54% of recipients clicking malicious links.
AI-generated phishing enables threat actors to spin up convincing login pages, clone trusted brands, generate personalized lures, and rotate domains in a few minutes or hours. Case in point: IBM’s X-Force Red Offensive Security Services was able to trick a generative AI model to develop highly convincing phishing emails in just five minutes with only five simple prompts.
But many organizations still rely on a response model designed for a different era: legal escalation under the Digital Millennium Copyright Act (DMCA).
When a phishing site appears, internal teams document infringement, route evidence to legal counsel, file a DMCA takedown request, and wait for a hosting provider to process it. That sequence doesn’t work against modern phishing infrastructure, where every hour of delay expands the window for credential theft, account compromise, and customer harm.
At Netcraft, our disruption teams see this gap constantly. Organizations still approach phishing like a copyright enforcement problem, even as attackers rotate infrastructure in hours instead of days. Across real-world investigations, we routinely hear security and legal teams describe the same frustration: by the time a DMCA request is processed, the campaign has already evolved or moved.
The DMCA Myth: Why Legal Notices Fail Phishing Victims
Many brands think their brand protection strategy is a legal one.
They believe that, if a competitor steals your website’s copy or uses your logo on their storefront, you have a copyright problem. You call a lawyer, file a DMCA notice, and wait for the legal process to take its course. It’s a battle over intellectual property, and the goal is to protect your "art."
That instinct makes sense in traditional infringement scenarios. Copyright and trademark frameworks exist to resolve disputes involving stolen creative assets, copied content, or unauthorized brand use.
But phishing isn’t a copyright problem.
When a criminal creates a pixel-perfect replica of your login page, they aren't "stealing your content" — they are weaponizing your identity to target your customers.
Attackers use your branding because that trust increases conversion rates. Familiar logos, login experiences, and customer communications lower suspicion and increase the likelihood of clicks, credential submission, or payment fraud.
The crime starts with stealing your logo and ends with tricking your customers into sharing credentials and data. And the damage occurs long before a legal review concludes. Every minute the infrastructure remains online increases exposure, financial loss, and reputational damage.
By the time the DMCA notice is processed, this industrialized fraud operation has already stolen thousands of credentials and moved on to a new domain.
Why the DMCA is the Wrong Tool for Phishing
Legal takedowns still have value in certain circumstances. They can remove infringing content and support enforcement efforts. But phishing infrastructure exposes several limitations that become increasingly costly in the age of AI-generated attacks.
The 72-Hour Victimization Window
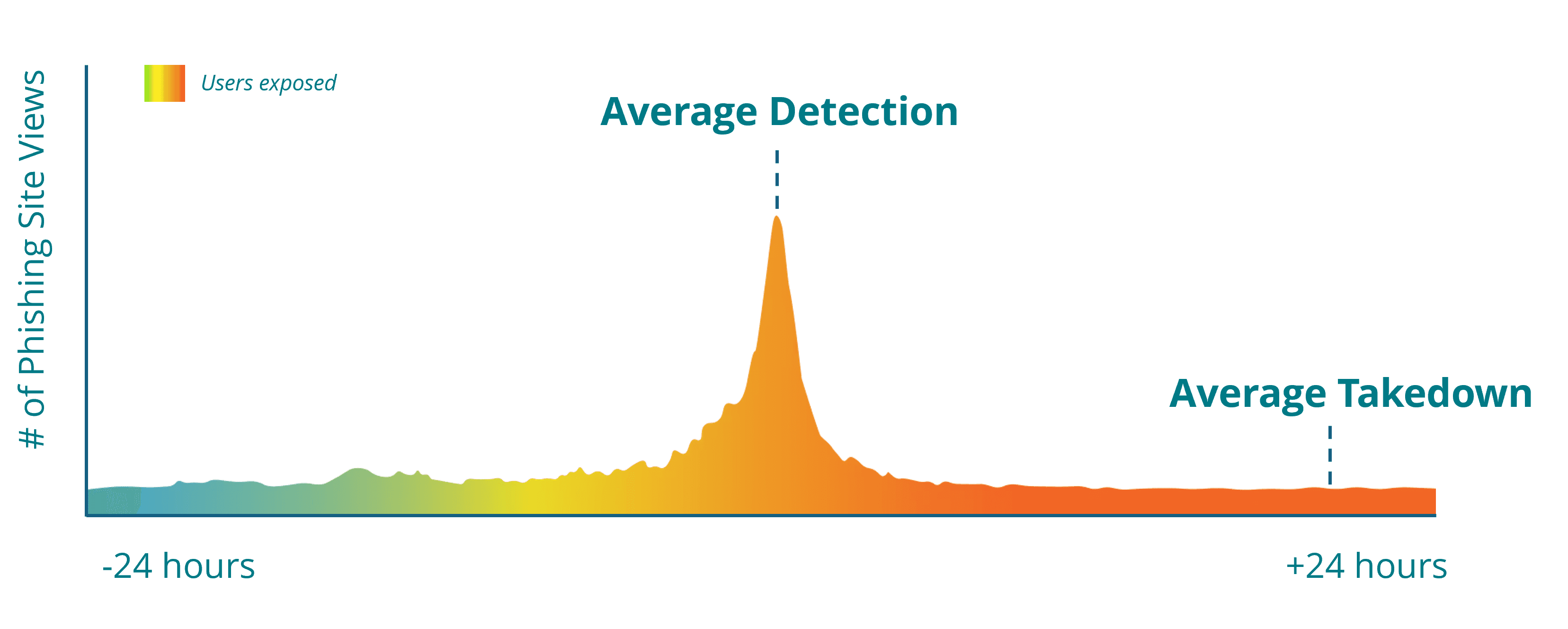
Our analysts regularly see phishing campaigns complete their most damaging phase long before traditional takedown workflows finish. In many cases, credential harvesting peaks within the first few hours after launch.
Figure 1: 95% of phishing site visits occur within 20 hours of detection.
DMCA processes depend on provider response timelines. Hosting companies, registrars, and platforms generally evaluate notices according to “reasonable response” standards.
In practice, that often translates into a 48–72 hour delay before action occurs. But many sites also say the average takedown time frame is within 10 business days for content removal.
This frustration comes up repeatedly in customer conversations. Security teams often tell us they feel trapped between fast-moving phishing campaigns and slow-moving administrative processes. One fast-growing direct-to-consumer brand described the challenge this way:
“We’ve submitted the DMCA and the other avenues you can go… they haven’t been taken down yet.”
For phishing operators, that timeline is more than enough to take advantage of unsuspecting victims. They can spin up phishing attacks, harvest credentials, compromise accounts and move on before legal workflows even begin to gain momentum.
The result is a dangerous victimization window: customers remain exposed while organizations wait for administrative processes to catch up.
DMCA Content Removal Leaves Phishing Infrastructure Standing
At the same time, DMCA notices focus on copyrighted material. If a copied logo or image is removed, the provider may consider the issue resolved — even if the phishing domain itself remains active.
Attackers understand this distinction, and our disruption teams see them exploit it constantly. When one asset is removed, attackers simply rotate logos, swap content, or redirect traffic while keeping the underlying infrastructure active. The infrastructure survives, the campaign continues, and the threat remains operational.
“We don’t kill the site. We only kill the symptom… we don’t heal the disease.”
This is how one large European brand described its experience with manually filing thousands of DMCA requests to remove stolen content from Google results.
What’s more, modern phishing infrastructure rarely behaves like a traditional business dispute. Domains are registered anonymously and hosting shifts rapidly between providers. A cease-and-desist letter carries little weight when attackers can’t be identified in the first place.
Don't Sue the Scammer. Break Their Tools
Phishing defense is an infrastructure problem. Success depends on identifying malicious systems and disrupting their ability to operate. Security teams need outcomes measured by neutralization, not documentation.
Our experience disrupting phishing campaigns at scale has shown that infrastructure providers respond fastest when abuse is framed as an operational threat rather than a copyright dispute. That’s why we focus on technical disruption. Instead of debating copyright infringement, Netcraft provides Verified Attack Indicators™ (VAIs) to hosting providers, registrars, and infrastructure partners. For preemptive use cases, these indicators provide verifiable evidence of abuse or strong indicators of criminal ties.
This distinction matters. Infrastructure providers respond differently when they receive evidence of active abuse tied to phishing, fraud, or malicious intent. Emergency enforcement can happen immediately because the issue becomes operational risk rather than legal interpretation. Rather than waiting for legal review cycles, malicious infrastructure can be disrupted at the platform level.
Online brand protection should also start before takedowns occur. Instead of waiting for sites to be removed, Netcraft uses fraudcasting to push protections to more than 1 billion browsers in minutes, blocking access to malicious destinations even before infrastructure is fully removed.
That means customers receive protection while investigations are still unfolding. Exposure shrinks dramatically because the attack becomes harder to reach, harder to scale, and harder to monetize.
From "Takedown" to "Disruption"
As AI-generated phishing makes attacks even easier to execute, effective phishing defense increasingly depends on stopping campaigns before they have a chance to mature.
Threat actors often prepare infrastructure days or weeks before launch. Domains are registered, DNS records configured, certificates issued, and environments staged for future abuse. Our teams increasingly observe attackers preparing and rotating phishing infrastructure well before campaigns become visible to targets.
This is why Netcraft has launched Preemptive Domain Disruption, a new AI-powered capability that allows organizations to disrupt malicious infrastructure before attacks are launched. Preemptive Domain Disruption enables Netcraft to "jump Left of Live™” — identifying domains configured for abuse before content even appears.
This capability matters because many legal mechanisms require visible infringement before action begins. A blank page offers little evidence for a traditional copyright claim. Security telemetry tells a different story.
Patterns in hosting, domain behavior, infrastructure relationships, and configuration signals can reveal malicious intent before a phishing page goes live. That early phishing detection allows defenders to intervene upstream and eliminate infrastructure before customers ever encounter it.
The goal shifts from reacting faster to preventing exposure entirely.
Comparison Table: DMCA Takedowns vs. Technical Disruption
Feature | DMCA / Legal Notice | Technical Disruption |
|---|---|---|
Trigger | Copyright infringement and violations | Verified malicious intent or ToS violation |
Response Time | Typically 48 to 72 hours (Minimum) | 33 minutes* |
Scope | Removes a specific image or page | Neutralizes the domain and blocks in-browser |
Enforcement | Legal compliance (Optional for some) | Automated disruption (Hard-coded into infrastructure) |
*33 minutes is Netcraft’s median phishing takedown time, which is the fastest in the industry. Takedown times vary by vendor.
Outpacing the Algorithm
AI has accelerated phishing at a pace traditional response models cannot match. In an era where AI can spin up 14 times more attacks than last year, the 72-hour "legal lag" of a DMCA notice is an eternity.
If your brand protection strategy relies on a manual paper trail, you’re just documenting how phishing harms your customers. And when protection depends on legal action, customers remain vulnerable during the most dangerous phase of an attack. By the time notices are reviewed, many phishing campaigns have already achieved their objective.
Strong digital risk protection requires defenders to think operationally.
Success is measured by how quickly malicious infrastructure becomes ineffective. Minutes matter more than paperwork. Disruption matters more than documentation.
Stop the clock on AI-generated fraud. Schedule a demo to see how Netcraft’s automated disruption can shrink phishing takedowns from days to minutes.
DMCA Takedown FAQs
What is a DMCA takedown?
A DMCA takedown is a legal request submitted under the Digital Millennium Copyright Act (DMCA) asking a hosting provider, platform, or service to remove copyrighted material being used without permission. Organizations often use DMCA notices to address copied branding, logos, images, or website content appearing on fraudulent or unauthorized sites.
Why are DMCA takedowns ineffective against AI-generated phishing?
DMCA takedowns were designed for copyright infringement, not fast-moving phishing infrastructure. AI-generated phishing campaigns can launch, harvest credentials, and rotate domains within hours, while DMCA response timelines often take 48–72 hours or longer. By the time legal notices are processed, attackers have often already moved to new infrastructure.
What is the “72-hour victimization window”?
The “72-hour victimization window” refers to the period between the launch of a phishing campaign and the time legal takedown processes are completed. During this window, customers remain exposed to credential theft, account compromise, and fraud while organizations wait for hosting providers or platforms to process DMCA notices
What is the difference between a DMCA takedown and technical disruption?
A DMCA takedown focuses on copyright or trademark infringement and typically removes specific content or assets. Technical disruption provided by digital risk protection vendors focuses on verified malicious activity and aims to neutralize phishing infrastructure directly by working with hosting providers, registrars, and platforms to disable malicious operations.
Why is phishing an infrastructure problem instead of a copyright problem?
Phishing attacks use stolen branding to impersonate trusted organizations and deceive victims into sharing credentials or financial information. The goal is fraud, not content theft. Even if copied logos or images are removed, the phishing infrastructure often remains active and continues operating.
What is technical disruption in phishing defense?
Technical disruption is the process of identifying and neutralizing malicious infrastructure used in phishing attacks. Instead of relying on legal escalation, defenders provide evidence of active abuse, phishing activity, or platform terms-of-service violations to infrastructure providers so malicious domains and services can be disrupted quickly.
What are Verified Attack Indicators (VAI)?
Verified Attack Indicators (VAI) are evidence-based indicators used to demonstrate that phishing, fraud, or other malicious activity is occurring. Netcraft provides these indicators to hosting providers, registrars, and infrastructure partners to support rapid disruption of malicious infrastructure
What is Preemptive Domain Disruption?
Preemptive Domain Disruption is Netcraft’s AI-powered capability designed to identify and disrupt malicious infrastructure before phishing attacks are launched. By analyzing hosting patterns, domain behavior, certificates, and infrastructure relationships, defenders can identify domains configured for abuse before phishing content becomes visible.
How quickly can phishing infrastructure be disrupted?
Phishing infrastructure can be disrupted in as little as minutes or take days or even weeks, depending on the approach, provider response times, and the vendor involved. Technical disruption methods designed around verified malicious activity typically move significantly faster than traditional legal or manual takedown processes.
How does AI-generated phishing change the threat landscape?
AI-generated phishing allows threat actors to create convincing phishing emails, clone trusted brands, generate personalized lures, and deploy malicious infrastructure at industrial scale. This acceleration reduces the effectiveness of traditional manual or legal-first response processes.
What is Digital Risk Protection (DRP)?
Digital Risk Protection (DRP) refers to strategies and technologies designed to identify, monitor, and disrupt digital threats targeting organizations and their customers, including phishing, impersonation, fraud, and malicious infrastructure.