Executive Summary
Platforms like Webflow are built to empower legitimate businesses by enabling anyone to launch polished, professional websites complete with HTTPS certificates in a matter of minutes. That same simplicity and accessibility can also lower the barrier for cybercriminal abuse.
Earlier reporting linked Webflow[.]io subdomains to cryptocurrency-related scams, including fraudulent “connect wallet” and airdrop pages. Netcraft’s recent investigation identified a notable shift toward Booking.com impersonation hosted on Webflow subdomains.
The observed pages leverage Webflow infrastructure and HTTPS certificates to appear legitimate while mimicking one of the world’s most recognized travel brands.
This activity reflects misuse of a legitimate website-building platform rather than wrongdoing by the provider itself. Netcraft maintains a constructive working relationship with Webflow and continues to collaborate with providers to identify, report, and reduce instances of platform misuse.
Booking DOT com Impersonation Campaign
Netcraft identified a cluster of Webflow-hosted subdomains impersonating Booking.com, many of which incorporate deliberate misspellings and travel-related keywords. One example, bookinggcomdubaflighttickets[.]webflow[.]io, visually mimics the Booking.com website while using a lookalike domain structure to exploit user trust.
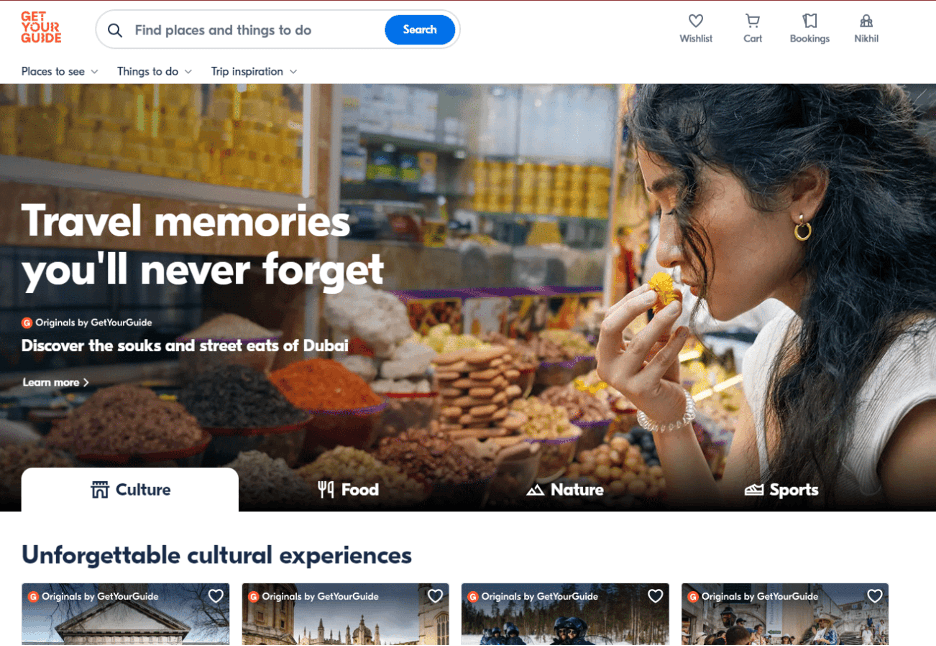
Figure 1. Booking.com impersonation page hosted on Webflow.
The page appears to function as a brand impersonation landing page designed to mislead users searching for Dubai travel bookings. While the visible interface closely resembles Booking.com, it is entirely static and implemented as a full-page image. Beneath this visual layer, keyword-dense travel content focused on Dubai attractions is embedded in the HTML, suggesting the page is optimized for search engine indexing rather than immediate credential harvesting.
Although no credential or payment form is present in the visible source code, it is realistically possible that this type of infrastructure supports phishing campaigns by building perceived legitimacy, potentially positioning users for later redirection or monetization.
Evidence of SEO Poisoning
The volume and structure of related domains suggest this activity may extend beyond traditional phishing into search manipulation tactics. Observed examples include:
booking-com-dubai-restttaurants[.]webflow[.]io
booking-com-dubbbbai-tickets[.]webflow[.]io
bookingggcomdubaiirestaurants[.]webflow[.]io
bookinggcomdubaiiitickets[.]webflow[.]io
help.booking-comdubaicom-packages[.]webflow[.]io
secure.booking-com-waedubai-hotels[.]webflow[.]io
booking--dubai--com[.]webflow[.]io
booking-ceom-duebai-tiec-kets[.]webflow[.]io
Many follow the same pattern: Booking.com branding combined with Dubai-specific travel terms and deliberate character substitutions. When initially identified, the majority of these subdomains returned 404 errors. They have since been populated with near-identical content, including keyword-heavy text and a full-page screenshot mimicking the Booking.com homepage, suggesting coordinated deployment rather than isolated abuse.
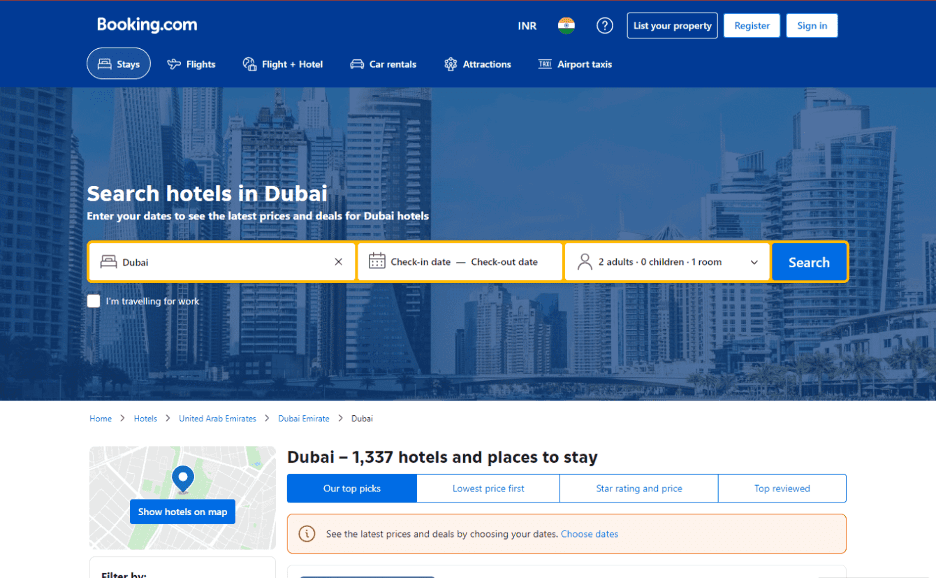
Figure 2. Related Webflow-hosted Booking.com impersonation content.
The consistent focus on Dubai between January and February 2026 may not be incidental. January and February fall within Dubai’s peak tourism season (November–March), when milder weather and increased travel activity drive higher visitor volumes. Early-year trip planning and spring break bookings can also drive higher search volumes for destination-specific queries such as “Dubai tickets” and “Dubai hotels.”
By aligning lookalike subdomains with high-intent travel keywords, threat actors may be attempting to capture seasonal search traffic. The use of static, image-based pages combined with keyword-heavy text suggests a dual-layer strategy targeting both human users and search indexing systems. This approach may contribute to SEO poisoning, increasing visibility of malicious infrastructure while creating noise around legitimate brand results.
Other Observed Abuse
While this blog focuses on Booking.com impersonation, Webflow-hosted abuse has also been observed targeting other verticals, including financial relief themes. One example, erc-national-payment-processing[.]webflow[.]io, imitates an ERC-related payment service using government and financial terminology to appear credible. Although no credential or payment form is present on the page, selecting “Sign Up” redirects users to iw[.]lendflow[.]com, a legitimate lending infrastructure platform. As platforms like Lendflow allow users to create and customize their own application workflows, this can make such setups appear more trustworthy, even when paired with deceptive branding at the initial entry point.
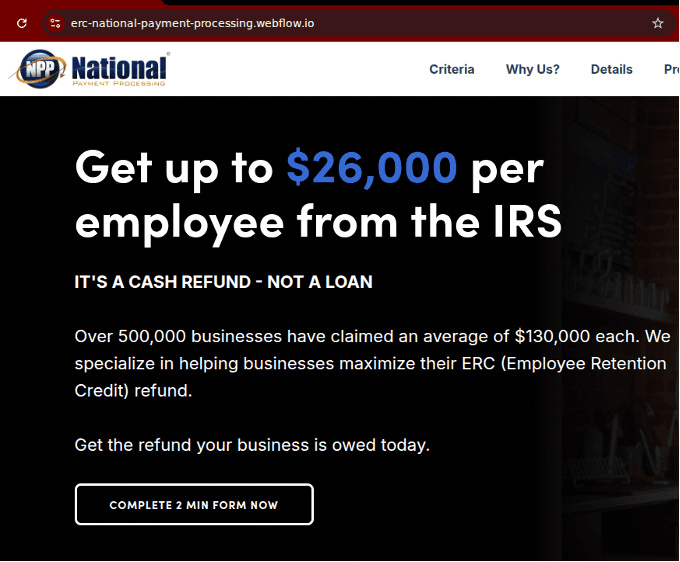
Figure 3. ERC payment service phishing page.
Looking Ahead
The observed Booking.com impersonation campaign demonstrates how threat actors can combine visual mimicry, lookalike domains, and search optimization tactics to build deceptive infrastructure at scale. Even when pages do not directly host credential forms, they may serve as staging layers within a broader phishing or traffic-manipulation strategy.
Organizations should consider the following defensive measures:
Monitor for lookalike subdomains hosted on legitimate website-building platforms.
Incorporate seasonal and destination-based keyword monitoring into brand protection strategies.
Report suspicious hosted content to platform providers promptly to limit exposure.
Educate users to verify domain names carefully, particularly during high-volume travel periods.
Indicators of compromise (IOCs) associated with this campaign are published in Netcraft’s public GitHub repository.




