Executive Summary
Netcraft researchers have identified an ongoing campaign involving the compromise and defacement of thousands of Magento ecommerce sites across multiple sectors and geographies.
Beginning 27 February 2026, attackers have deployed defacement txt files across approximately 15,000 hostnames spanning 7,500 domains, including infrastructure associated with prominent global brands, e-commerce platforms, and government services.
While a small number of defacements included geopolitical messaging, the majority appear to be opportunistic compromises carried out for attribution and reputation within the defacement ecosystem, rather than targeted hacktivism.
Initial investigation indicates that the affected sites are running Magento, and the defacements appear to demonstrate the defacer’s ability to upload plaintext files to publicly accessible web directories. It is not yet confirmed whether this behavior is linked to a specific Magento vulnerability or misconfiguration.
Netcraft Observations
Netcraft detected this campaign’s first activity on 27 February 2026, with newly compromised sites continuing to appear at the time of writing.
Netcraft is tracking this campaign’s activity over 15,000+ hostnames (subdomains) within ~7,500 unique domains. Defacements were uploaded as plaintext files hosted directly on affected infrastructure.
The primary handles observed in the defacement pages include:
L4663R666H05T
Simsimi
Brokenpipe
Typical Idiot Security
These identifiers frequently appear alongside “greetz” lists — a hallmark of the website defacement subculture where attackers publicly acknowledge collaborators or affiliated groups.
Defacement Content and Messaging
Most compromised sites hosted a simple defacement txt file containing the attacker handles.
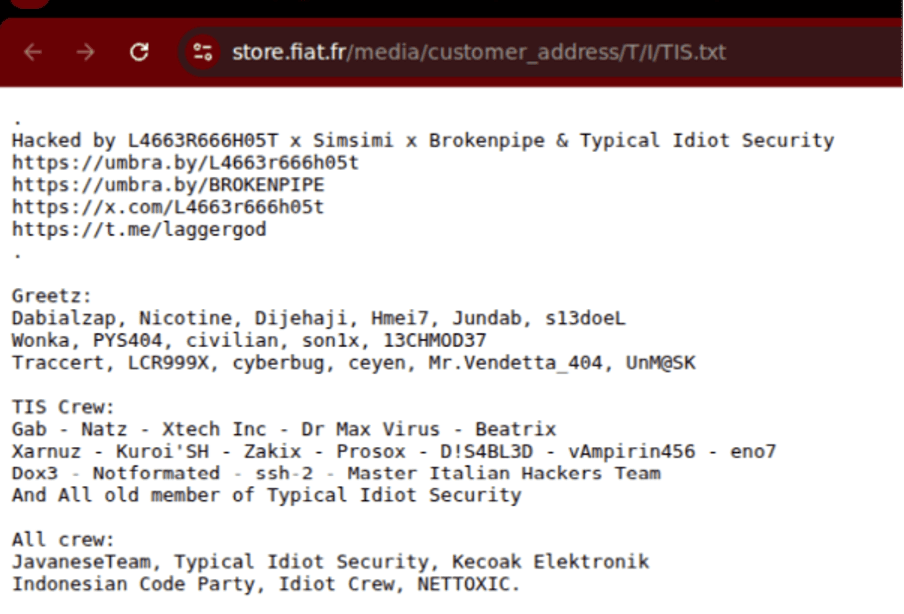
Figure 1. Example defacement page displaying attacker aliases and “greetz” message.
Limited Geopolitical Messaging
A small subset of defacements (fewer than 10 detected so far) included political messaging referencing recent geopolitical conflicts.
At the time of publication, these messages appeared only a single day, 7 March 2026. They were not present in earlier or later defacements, suggesting that this was not the primary motivation of the campaign.
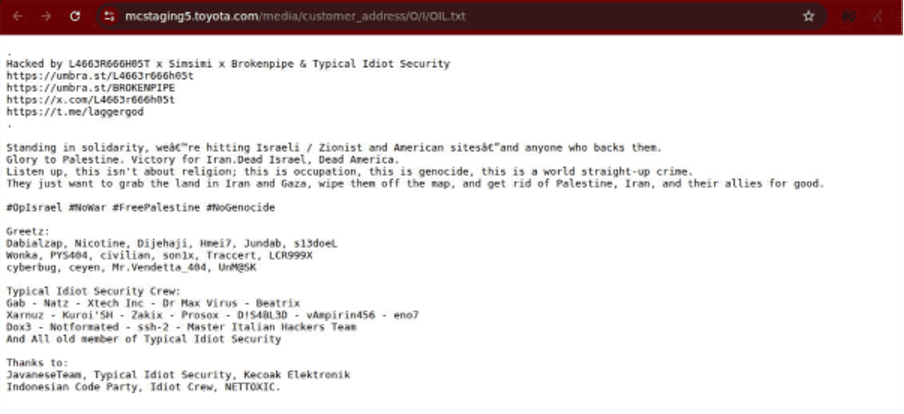
Figure 2. Defacement page containing geopolitical messaging observed on a limited number of compromised sites.
Attribution Signals
Many of the compromised pages have been reported to the defacement archive Zone-H, a long-running platform used to track defacement activity.
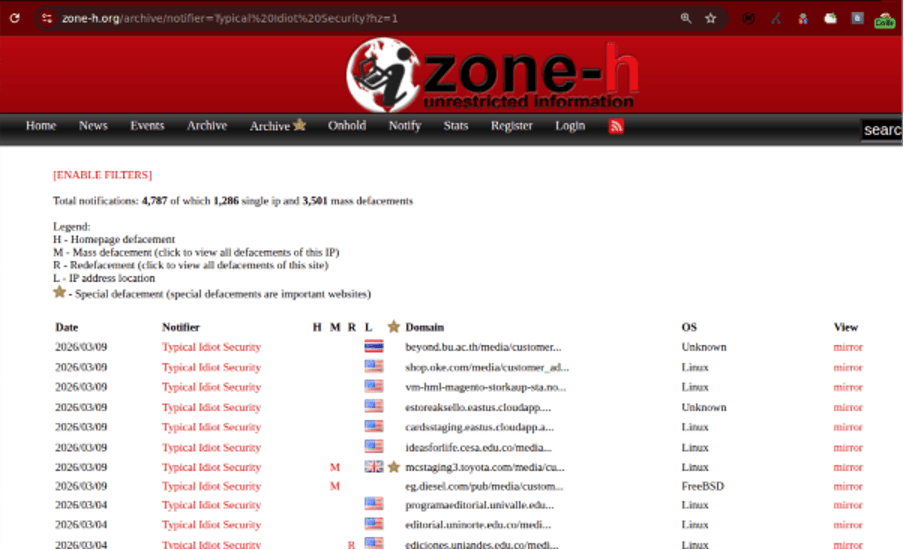
Figure 3. Pages reported to Zone-H by the notifier “Typical Idiot Security.”
Notably:
The Zone-H notifier account submitting the defacements is “Typical Idiot Security.”
This alias is also embedded directly in the defacement page content.
This overlap suggests the actor responsible for the defacement may also be self-reporting the compromises to build reputation within the defacement community.
Suspected Exploitation of Magento Infrastructure
Initial investigation suggests attackers may be abusing an unauthenticated file upload associated with some, but not all, Magento environments. As of the time of this publication, Netcraft has uncovered only text-based file defacements.
Magento variants observed in affected environments include:
Magento Open Source (Community Edition)
Magento Enterprise / Adobe Commerce
Adobe Commerce deployments with Magento B2B
Adobe recently released a security bulletin addressing multiple Adobe Commerce vulnerabilities, though the published details do not appear to be directly linked to the behavior observed in this campaign.
This campaign appears to use a similar modus operandi to that noted by other cybersecurity companies detailing the SessionReaper Magento vulnerability in October 2025. Netcraft was able to upload a .txt file to a test Magento instance running the latest version at the time of publication, Magento Community 2.4.9-beta1.
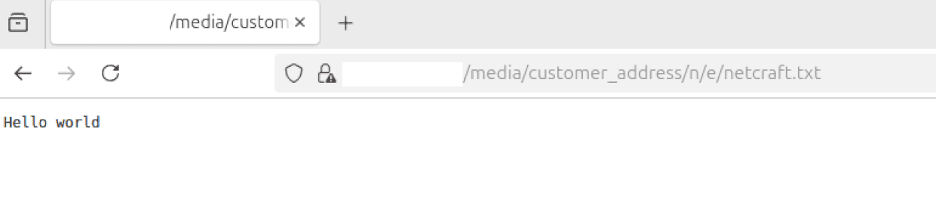
Figure 4. Text file uploaded to a test Magento Community instance by Netcraft.
Magento remains one of the most widely used e-commerce platforms globally, powering both small storefronts and enterprise commerce deployments.
High-Profile Organizations Affected
The campaign impacted infrastructure belonging to several globally recognized brands.
Affected organizations include:
Toyota
Fiat
Citroën
Asus
Diesel
FilaBandai
FedEx
BenQ
Yamaha
Lindt
In many cases the compromises occurred on subdomains, staging environments, or regional storefronts, though some production-facing sites were briefly affected before remediation.
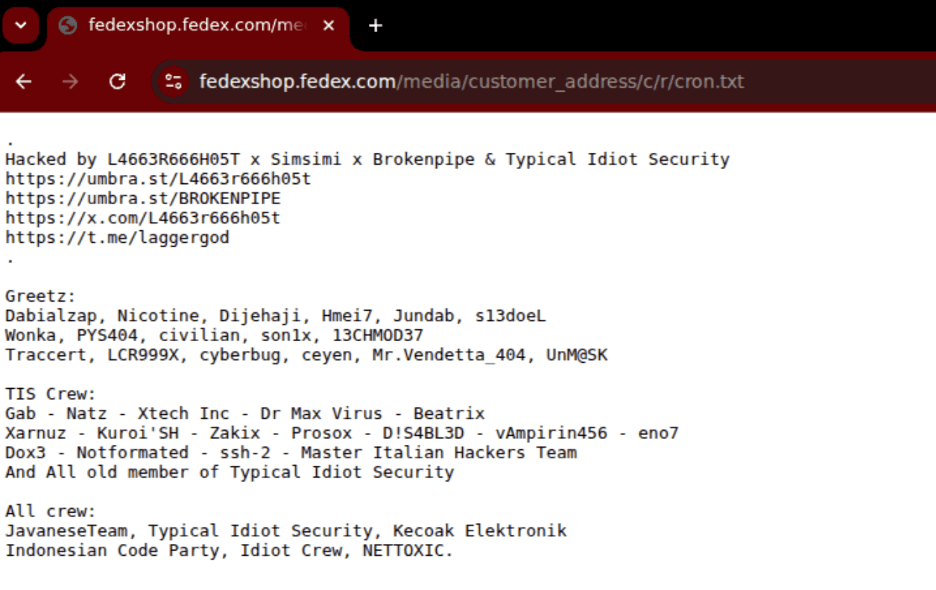
Figure 5. Defacement observed on an e-commerce storefront environment.
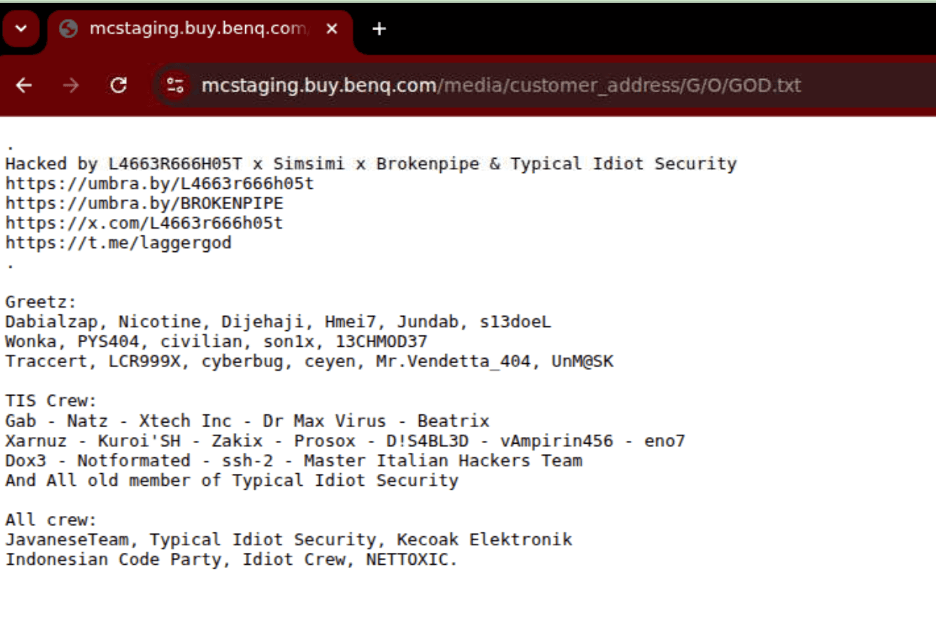
Figure 6. Example of a compromised staging or regional storefront domain.
Government and Institutional Domains
The campaign also affected several public sector and academic domains.
These included:
Regional government services
University domains in Latin America and Qatar
International non-profit infrastructure
As with commercial organizations, most compromises appear to involve web infrastructure rather than core systems.
Trump-Related Infrastructure
Researchers also identified defacements affecting several domains associated with the Trump Organization, including:
trumpstore.com
trumphotels.com
booktrump.com (including regional booking subdomains)
However, based on the pattern of compromises observed across thousands of domains, these sites do not appear to have been singled out. Instead, they were likely affected as part of broad exploitation against vulnerable infrastructure.
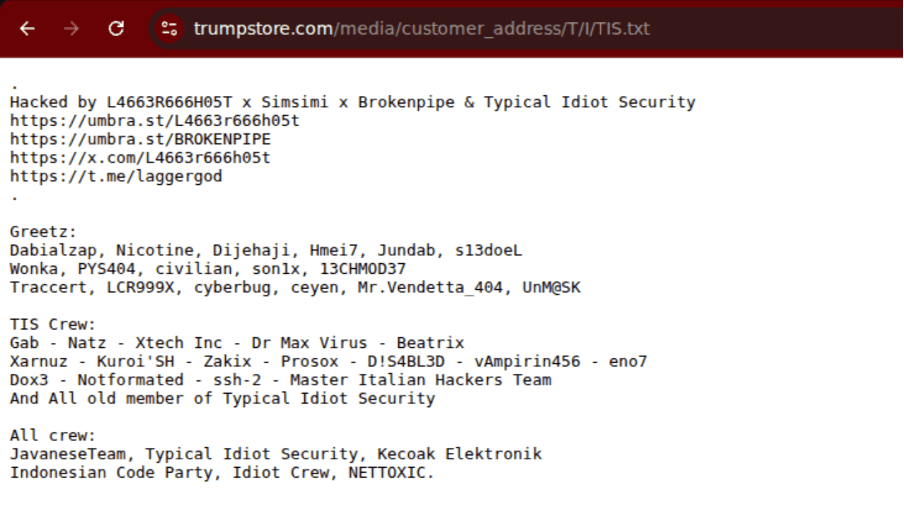
Figure 7. Example defacement hosted on infrastructure linked to the Trump Organization.
What Is Website Defacement?
Website defacement involves compromising a website and replacing or adding visible content controlled by an attacker.
The attackers, known as defacers, often aim to:
Demonstrate technical capability
Publicly claim responsibility for compromises
Deliver political or ideological messaging
Accumulate defacement counts in public archives
Defacers often use websites such as Zone-H (http://www.zone-h.org/) to keep an archive of their defacements. These websites also typically track number of defacements by each user or group, and in some cases a separate tally of defacements of important websites e.g. governments. The website Zone-H likens this website defacement to virtual graffiti.
Because defacement campaigns frequently rely on mass exploitation of common software vulnerabilities, attackers can compromise large numbers of sites in a short period.
Ongoing Activity
Netcraft continues to observe new defacements attributed to the same attacker handles, suggesting the campaign remains active at the time of publication.
Organizations running Magento infrastructure should:
Review exposure of file upload endpoints
Apply the latest Adobe Commerce security updates
Monitor web infrastructure for unauthorized file uploads
Investigate unexpected files appearing in web directories
Given the scale of the activity and the number of high-profile domains affected, this campaign highlights how widely deployed web platforms can become a force multiplier for attackers conducting opportunistic exploitation.





